Google announced on Thursday that it’s taking action against misleading and malicious notifications in Chrome with the release of version 84, which is scheduled for July 14.
Browser notifications can be useful for certain types of services but some websites abuse them to mislead users, deliver malware, or phish personal information.
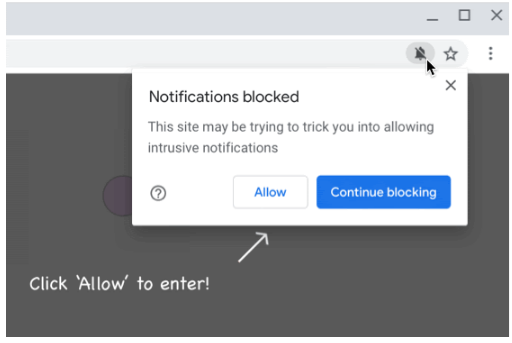
Google classifies abusive notifications as permission request issues, which trick or force users into allowing notifications, and notification issues, which are fake messages that mimic chats, system dialogs or warnings. The latter can be used for phishing and to distribute malware.
Starting with Chrome 84, websites that push abusive notifications will be automatically enrolled in the quieter notifications user interface, which Google introduced in January. This feature prevents notification permission requests from being displayed — the user is informed that a notification was blocked via a discreet message in the address bar in an effort to ensure that browsing is not disrupted.
Chrome 84 will also display alerts informing users that a notification was blocked as it may be trying to trick them. Users have to click an “Allow” button to see the blocked notification.
“Abusive notification protection in Chrome 84 will only affect new notification permission requests from abusive sites. In the future, we may add protections for users who have already accepted notification permissions from abusive sites,” Google explained in a blog post.
The tech giant has advised website owners to check the Abusive Notifications Report in their site’s Search Console to see if their website displays what Google would classify as an abusive notification. The company also provides information on how to address such problems.
“The first time a site is found to be in ‘Failing’ status, Search Console will send an email to registered site owners and users in Search Console at least 30 calendar days prior to the start of enforcement. Websites will have the opportunity during this time period to address the issue and re-submit their website for another review,” Google explained.
Related: Chrome 83 Brings Enhanced Safe Browsing, New Privacy and Security Controls
Related: Google Boosts Site Isolation in Chrome
Related: Google Boosts Chrome Protection Against Deceptive Sites












