Google announced this week that it will expand Safe Browsing on macOS in an effort to protect Chrome users against unwanted ad injections and unauthorized settings changes.
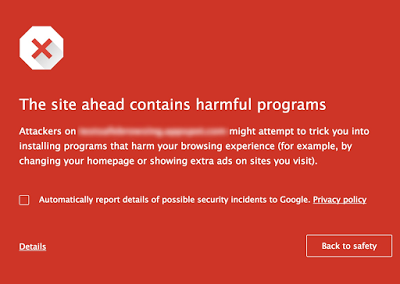
“Safe Browsing is broadening its protection of macOS devices, enabling safer browsing experiences by improving defenses against unwanted software and malware targeting macOS,” Google’s Kylie McRoberts and Ryan Rasti said on the company’s Security Blog. “As a result, macOS users may start seeing more warnings when they navigate to dangerous sites or download dangerous files.”
Applications that inject ads violate Google’s unwanted software policy and Mac users will be warned when Chrome detects such activity.
As for Chrome settings, the tech giant wants to ensure that applications cannot make unauthorized changes to the start page, the home page and the default search engine.
Google recently launched a new Mac API called Settings Overrides, which allows Chrome extensions to override the start page, home page and search settings in the web browser. The company wants this API to be the only approved method for making changes to Chrome settings on macOS and OS X.
However, only extensions approved for the Chrome Web Store are allowed to use the Settings Overrides API. Starting with March 31, Chrome will display a warning when a piece of software attempts to modify settings via other methods.
Related: Google Improves Safe Browsing for Network Admins
Related: Google Optimizes Safe Browsing API for Mobile











