Cybercriminals claim to have breached systems belonging to France’s Ministry of Justice and they are threatening to make public the files stolen from the government organization.
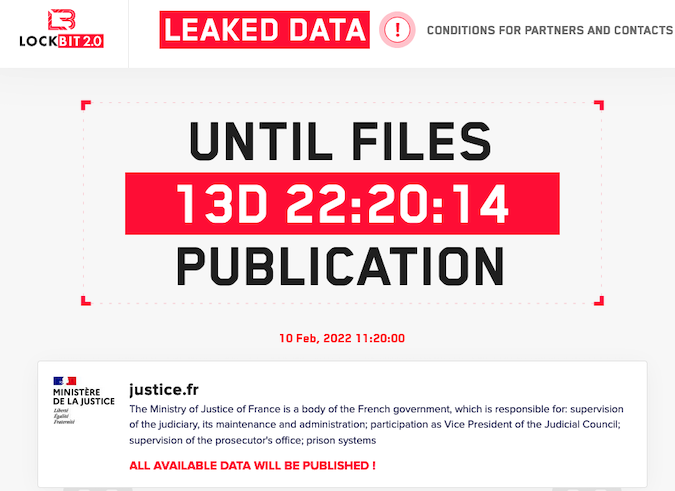
Threat actors who are using the ransomware named LockBit 2.0 have posted a message on their Tor-based leak website claiming to have stolen files from the Ministry of Justice’s systems.
The ministry’s press office told SecurityWeek that an investigation has been launched.
“The French Ministry of Justice is aware of the alert and has immediately taken actions to proceed to the needed verifications, in collaboration with the competent services in this field,” the statement reads.
The hackers state on their website that an unspecified amount of stolen data will be made public in two weeks from now, on February 10.
Cybersecurity researcher Anis Haboubi told SecurityWeek that the government organization failed to secure its BIG-IP instances. The researcher believes the attackers may have exploited CVE-2021-22986, an unauthenticated remote command execution vulnerability that F5 patched in March 2021.
Following reports of the attack, journalist Emile Marzolf pointed out on Twitter that a recent report from France’s Court of Audit revealed cybersecurity problems at the Ministry of Justice.
LockBit 2.0 operators also targeted Danish wind turbine giant Vestas and consulting giant Accenture in the past. They are known to leak files stolen from victims that refuse to pay a ransom.
Authorities around the world have stepped up efforts against ransomware operators following a series of damaging attacks.
In response to mounting pressure, even Russia has started taking action against citizens believed to be involved in cybercrime operations. The country’s FSB security agency announced recently the arrests of over a dozen people believed to be members of the REvil group. However, REvil operations are apparently unaffected by the arrests.
*updated with information from Anis Haboubi
Related: IT Services Firm Inetum Discloses Ransomware Attack
Related: Australian Electricity Provider ‘CS Energy’ Hit by Ransomware
Related: Logistics Firm Hellmann Scrambling to Recover From Cyberattack















