Consulting giant Accenture on Wednesday confirmed being targeted by hackers. The confirmation came just hours before a ransomware gang started leaking files allegedly stolen from the company.
The incident came to light when LockBit ransomware operators claimed on their website that they had breached Accenture’s systems. A counter displayed on the site showed that stolen files would be made public within hours, unless Accenture paid up.
“Through our security controls and protocols, we identified irregular activity in one of our environments. We immediately contained the matter and isolated the affected servers. We fully restored our affected systems from back up. There was no impact on Accenture’s operations, or on our clients’ systems,” Accenture stated.
LockBit ransomware operators encrypt files on compromised systems, but before doing so, they typically spend days or weeks on the victim’s network to harvest potentially valuable information that they can use to extort the target and increase their chances of getting paid.
When the time ran out on their website, the hackers made public more than 2,000 files allegedly stolen from Accenture. The company has yet to make any comments on the files being leaked, but people who have analyzed the exposed files said they do not appear to store customer information.
On the other hand, more files could be made public soon. Cyber risk intelligence company Cyble said the cybercriminals claimed to have obtained more than 6 Tb of files and they demanded a $50 million ransom from Accenture.
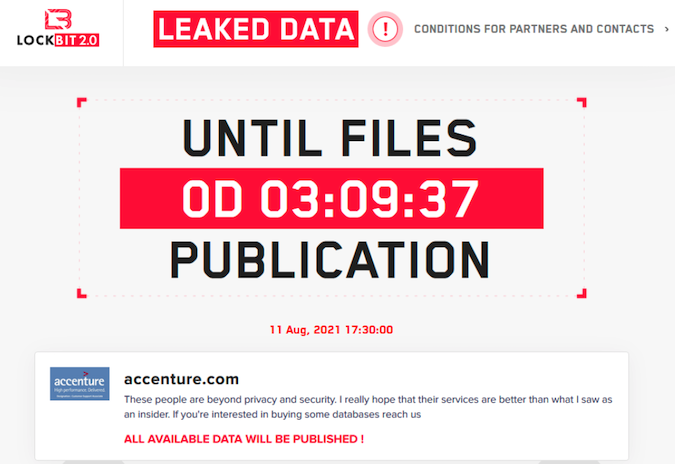
The hackers suggested on their website and elsewhere that they were helped by an insider, specifically someone who is still employed by the company. Cyble said LockBit operators had been looking to hire corporate employees that would help them gain access to their targets’ networks.
The LockBit ransomware has been around since 2019, with version 2.0 being launched earlier this summer. The malware has been used in attacks aimed at thousands of organizations. Australia’s Cyber Security Centre reported earlier this month that LockBit operators had been exploiting an old vulnerability affecting internet-exposed Fortinet devices for initial access.
Felipe Duarte, security researcher at secure access firm Appgate, told SecurityWeek that the recently introduced LockBit 2.0 implemented several new features that made it even more dangerous.
“Among the advertised capabilities is a new dangerous feature to encrypt entire Windows domains through group policies. After infecting a domain controller, the malware creates new group policies and pushes them to every device connected on the network. Those policies disable antivirus protections and execute the ransomware. Additionally, LockBit seems to have copied a feature from Egregor ransomware, that after a successful infection, it sends to all connected printers a command to repeatedly print the ransom note,” Duarte said.
“LockBit’s new version also added a new strategy to acquire ‘affiliates’,” the researcher added. “After encrypting a device, LockBit sets the wallpaper to a ransom note, claiming responsibility for the attack and pointing to the more detailed ransom note .txt file. Now the set wallpaper also contains a recruitment ad, promising millions of dollars to employees that provides them access to the company systems so they can launch a ransomware attack. According to the ad, the access can be a valid credential or even executing a threat attached in an e-mail.”
Related: IT Software Firm Kaseya Hit By Supply Chain Ransomware Attack
Related: DarkSide Ransomware Hits Toshiba Tec Group
Related: Bose Says Personal Information Compromised in Ransomware Attack

