In-the-wild exploitation of a Fortinet FortiNAC vulnerability tracked as CVE-2022-39952 was seen just days after a patch was announced, and on the same day a proof-of-concept (PoC) exploit was made public.
Fortinet published 40 security advisories on February 16, including one describing a critical vulnerability in the company’s FortiNAC network access control (NAC) solution. The security hole was discovered internally by Fortinet.
The flaw, an external file name and path control issue, can be exploited by an unauthenticated attacker to write data on a system, which can result in arbitrary code execution.
On February 21, autonomous pentesting company Horizon3 released a blog post detailing how CVE-2022-39952 can be exploited and also released a PoC exploit.
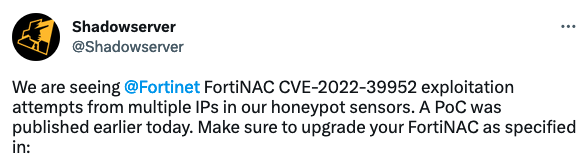
On the same day, the nonprofit cybersecurity organization Shadowserver warned that its honeypots had started seeing exploitation attempts coming from multiple IP addresses.
On February 22, threat intelligence company GreyNoise also reported seeing broad exploitation of the FortiNAC vulnerability. The firm has so far seen attacks coming from two IPs.
Chile-based cybersecurity firm Cronup also reported seeing mass exploitation on February 22, with attacks coming from 10 IP addresses. While some attempts appear to be designed to identify vulnerable FortiNAC systems, others deploy a reverse shell.
Several Fortinet product vulnerabilities have been exploited in attacks in the past years. The US Cybersecurity and Infrastructure Security Agency (CISA) lists nine such flaws in its known exploited vulnerabilities catalog.
The most recent is CVE-2022-42475, which has been leveraged by a China-linked threat actor in attacks aimed at government organizations in Europe.
Related: Fortinet Ships Emergency Patch for Already-Exploited VPN Flaw
Related: High-Severity Command Injection Flaws Found in Fortinet’s FortiTester, FortiADC
Related: Fortinet Confirms Zero-Day Vulnerability Exploited in One Attack

