Fortinet released 40 security advisories last week to inform customers about the availability of patches for dozens of vulnerabilities, including critical flaws affecting the FortiNAC and FortiWeb products.
Two of the advisories have a ‘critical’ severity rating and 15 of them have been classified as having ‘high’ severity.
One of the critical advisories describes CVE-2021-42756, a CVE identifier assigned to multiple stack-based buffer overflow vulnerabilities in FortiWeb’s proxy daemon. The security holes can allow a remote, unauthenticated attacker to execute arbitrary code on the targeted system using malicious HTTP requests.
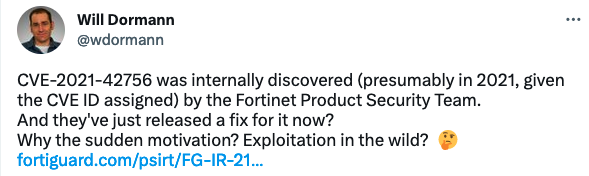
Based on its identifier, CVE-2021-42756 was discovered more than one year ago. It’s unclear why Fortinet has waited until now to patch it, but given its severity rating, some have speculated that potential exploitation in the wild could be a reason.
The second critical advisory describes CVE-2022-39952, an external file name or path control issue in FortiNAC that can allow an unauthenticated attacker to write data on a system, which could result in arbitrary code execution.
Autonomous pentesting company Horizon3 announced that it will soon release a blog post detailing how CVE-2022-39952 can be exploited for remote code execution with root privileges. Horizon3 also plans on releasing a proof-of-concept (PoC) exploit.
Threat intelligence company GreyNoise has used information provided by Horizon3 to start monitoring the internet for attacks exploiting the vulnerability. At the time of writing, there do not appear to be any attack attempts targeting CVE-2022-39952.
There are hundreds of thousands of Fortinet systems that are exposed to the internet and many of them could be vulnerable to attacks exploiting CVE-2022-39952.
Fortinet’s advisories for CVE-2021-42756 and CVE-2022-39952 currently do not mention anything about exploitation in the wild.
The high-severity vulnerabilities for which patches were announced last week impact products such as FortiADC, FortiExtender, FortiNAC, FortiOS, FortiProxy, FortiSwitchManager, FortiWAN, and FortiWeb.
They can be exploited to execute arbitrary code with elevated privileges, execute arbitrary OS commands, perform administrative operations, obtain user passwords, launch XSS attacks, read and write files on the underlying Linux system, and hijack sessions, but many require authentication.
The critical and many of the high-severity vulnerabilities were discovered internally by Fortinet.
It’s not uncommon for threat actors to target Fortinet product vulnerabilities in their attacks so it’s important that users install the patches as soon as possible.
One of the most recent actively exploited vulnerabilities is CVE-2022-42475, which has been leveraged by a China-linked threat actor in attacks aimed at government organizations in Europe.
Related: Fortinet Ships Emergency Patch for Already-Exploited VPN Flaw
Related: High-Severity Command Injection Flaws Found in Fortinet’s FortiTester, FortiADC
Related: Fortinet Confirms Zero-Day Vulnerability Exploited in One Attack

