Financially motivated attackers have become just as sophisticated as threat actors sponsored by nation states, according to the 2017 M-Trends report published on Tuesday by FireEye-owned Mandiant.
The report, which is based on data from actual incidents investigated by the company, shows that profit-driven cybercriminals have become increasingly sophisticated over the past few years.
Until 2013, cybercriminals mostly launched what experts described as “smash and grab” attacks – little effort was put into hiding their actions and maintaining access to the breached system. In the following years, the line between the level of sophistication exhibited by financial attackers and nation-state actors became increasingly blurry, and now researchers say that line no longer exists.
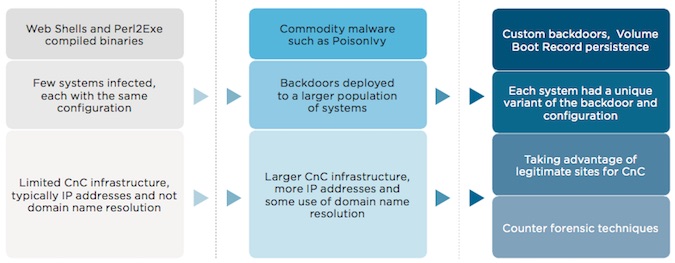
Financially motivated hackers went from using web shells and Perl2Exe compiled binaries with a limited command and control (C&C) infrastructure to using custom backdoors tailored to the targeted system and leveraging legitimate websites for C&C communications.
One interesting trend observed by Mandiant in 2016 was related to malicious macro-enabled documents. While in many cases attackers attempt to convince targeted users to enable macros by providing instructions in an email or the document itself, in some of the campaigns observed by researchers last year, hackers called victims on the phone to convince them to enable macros.
Retailers can be highly lucrative targets, especially since many of them fail to ensure that their networks are segmented, allowing attackers to breach the entire PCI environment once they have gained access to PoS systems in one location.
Since these attacks can be lucrative, cybercriminals put a lot of effort into them. In one of the attacks investigated by FireEye, a group that targeted more than 100 companies exploited a Windows zero-day vulnerability to escalate privileges on compromised systems.
Cybercriminals also leveraged sophisticated techniques to evade detection and ensure persistence. One of the most interesting methods involved modifying the volume boot record (VBR) to load backdoors before the operating system booted.
FireEye has also analyzed attacks targeting banks. In one incident at a bank in Asia, investigators discovered 96 compromised servers and workstations. The attackers breached a subsidiary’s network and from there they moved to the bank’s infrastructure.
In an attack aimed at a bank in the EMEA region, threat actors hacked into 45 servers and workstations using PowerShell and Metasploit for lateral movement. The attacker used hijacked accounts to initiate transfers of millions of dollars, and then wiped event logs and reformatted system volumes to cause disruptions in an effort to prevent the bank from identifying the fraudulent transactions before the process was completed.
According to FireEye, organizations have been more efficient in identifying breaches themselves, with the global median time from compromise to discovery dropping from 146 days in 2015 to 80 days in 2016. In the Americas, this dwell time was 35 days, but it was much higher in APAC countries, likely due to “lack of investment in security.”
“With an increased willingness of both nation-state and financial threat actors to operate increasingly blatant business disruption, extortion, and public disclosure attacks, fundamental protections such as data and key application segregation, network segmentation, and continuous visibility and monitoring of critical systems have returned to prominence and should remain a primary focus for many IT and security teams,” experts said in the report.
The full M-Trends 2017 report is available online in PDF format.













