Hundreds of protesters stormed the U.S. Capitol on Wednesday just as the House and Senate were certifying the election victory of Joe Biden. While much of the focus was on the physical destruction caused by the protesters, many people have pointed out that rioters gained access to computers in the Capitol, which in some cases were still turned on and logged in, as their users were forced to quickly evacuate.
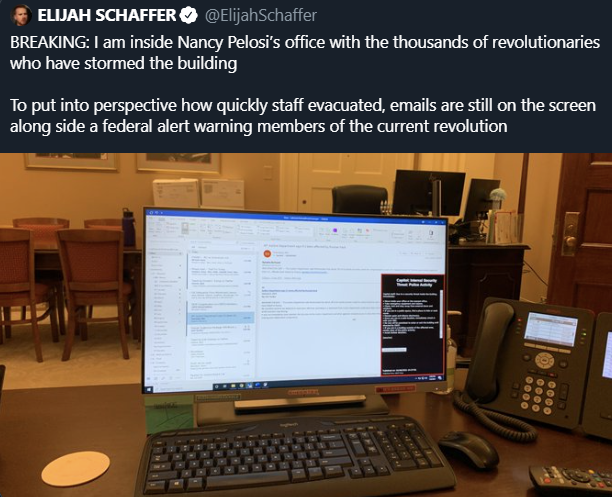
One man posted a tweet — it was later deleted but many Twitter users saved it before it was removed — showing him in front of an unlocked device allegedly belonging to someone in the office of House Speaker Nancy Pelosi. The picture showed someone’s email account open on the computer.
In addition to the physical documents and laptops that some protesters removed from the Capitol, cybersecurity experts have raised concerns about what they may have or could have also done with the computers left inside the building.
Some pointed out that they could have accessed sensitive information and others warned that all devices should be considered compromised as the people who breached the Capitol could have planted malware or spying hardware. Others doubted that the rioters had the intent or knowledge to conduct these types of activities.
However, while there is no evidence of such activities to date, the incident highlighted that some organizations should prepare for situations where employees could be forced to suddenly abandon their workstations.
SecurityWeek has reached out to several experts, asking them what prevention and response strategies and policies they would implement if they were in charge of cybersecurity at such an organization.
James Arlen, CISO at Aiven:

“Preparatory training is vital as a baseline part of your security awareness program – when you leave your desk, lock your machine! Winkey-L or Ctrl-Cmd-Q for your Windows and Mac users should be a reflex. As you work through your program maturity, being able to remotely lock and wipe machines once staff has reached safety should be part of your technical bag of tricks.
Depending on the adversary in your threat model, your response after the fact would range from nothing at all to a complete rip & replace of all equipment from the keyboard to the Ethernet cable. Remember that physical access is everything! I think the first tweet I saw along these lines was from my good friend Gillis Jones (@gillis57) suggesting that everything in The Capitol should be replaced and it’s a very valid point.
Of course, I hope that you’re also following a proper 3-2-1 backup plan and the complete loss of multiple computer systems is annoying rather than devastating. Maybe it’s time to add a “site contamination” scenario to your Business Continuity Plan tabletop exercises – could you restart your operations with a corporate credit card and a Best Buy? You should be able to!”
Dirk Schrader, Global Vice President at New Net Technologies (NNT):

“There are quite a few situations which can force an organization’s employees to leave their workplace immediately, leaving their computers unattended.
For IT administrators, it also means leaving the company’s IT infrastructure of servers, access points, switches and routers behind. The strategy for such a situation includes planning, preparation and dry-runs, and monitoring. Planning starts as a tabletop exercise, defining what kind of event would force the workforce to leave, which systems should be locked automatically, or even shut down, how can this be triggered and monitored, what kind of data must be secured (perhaps in an encrypted way). Preparation for such an event should include, next to the appropriate training of staff on how to evacuate safely, automatic procedures to lock accounts (either after timeout or via a centrally triggered event), to secure servers by closing sessions and initiating graceful shutdowns where needed. Keeping it simple, automated is key, the more employees would have to do, to remember, the less it will work. Still, even the simplest of procedures needs rehearsal, so try it, tune it, identify short comings and fix them.
Once the situation is cleared, IT administration and IT security will work backwards, get the infrastructure and work stations back online while checking them. For this to be comprehensive, the monitoring is necessary. They need to be able to review logs provided by core technical controls, both built-in to operating systems but also by change control solutions. The task is two-folded, protect the workforce by making it less complicated for them to leave computers, but also make sure that no malicious activity which might have happened during a stress situation goes undetected.”
Jerry Ray, COO of SecureAge:

“I would have simply installed any tool that would prevent the exfiltration of plain data.
There are plenty of physical recommendations, such as having some type of smart card or USB token that can be removed in a second and prevent the removal or even viewing of any plain data. Even the rapid unplugging of a system would be useful if the data could not be extracted, as above.
But any physical policies quickly break down when scenarios include occupiers getting to systems before the users can depart. They could be taken hostage or simply be forced to leave the premises without touching anything. In such a case, the proactive encryption would still be enough to prevent both exfiltration or unauthorized access of any data.
If the data was also resident only on a remote server and not stored on the endpoint, that would help even more. Remote file servers could be shut down outside the facility while the proactive encryption protects whatever was resident and open on the endpoint.”
Kelvin Coleman, Executive Director of the National Cyber Security Alliance:

“As is the case with most prevention and response plans, nothing is ever foolproof. I think the overarching philosophy should always be about minimizing risk. Organizations — and security pros within those organizations — should be putting measures in place that can bring the potential for vulnerabilities as close to zero as humanly possible.
That said, deterrent strategies for this sort of scenario should be preemptive from the outset and begin with increased education and awareness for employees about the dangers of leaving sensitive data unprotected on idle endpoints and the vulnerabilities that creates for the organization as a whole. Those education initiatives should be woven into company culture and drilled on a regular basis. Subsequently, I would make sure that the organization has a sufficient incident response strategy in place and policies that adhere to trusted cybersecurity frameworks and protocols (e.g as outlined by NIST) in case any sensitive data is ever compromised or stolen (and chances are it will be at some point).
On the hardware and software front, businesses need to make sure employees are issued endpoints (laptops, mobile devices, etc) that are properly equipped to access and store company data in a secure way. Any previously issued hardware that isn’t properly outfitted should be recalled and updated. That means multi-factor authentication, file-level encryption solutions, secure VPN access and perhaps even biometric login solutions. Also, security teams/SOCs should be outfitted with a robust IT tech infrastructure that can allow for precise network monitoring and policy management across all employee devices, as well as accurate recording login attempts and timestamps associated with those attempts. This will make it easier to map a timeline of unauthorized access to any devices after theft occurs.”
Rajiv Kanaujia, VP of Operations at CloudCheckr:

“For organizations that don’t have business continuity plans (BCP) in place, it will be very difficult to develop and execute on a BCP at such short notice. The most important item at hand is the physical security of the employees. On the other hand, living with the COVID-19 situation for almost a year, most of the organizations have shifted to some form of remote culture.
The preventative strategy is to plan for a remote working event and sudden evacuation. Assuming you have not lost the physical security controls and the issues are personal safety only, you should instruct employees to leave the premises immediately and let the physical security team manage the perimeter, while in coordination with law enforcement teams. If employees cannot leave premises due to escalated physical safety situations, employees must be allowed to remain on the premises until the evacuation in coordination with law enforcement teams is possible.
Employees must then be tooled with laptops and zero-trust solutions so that they can work remotely. Laptops must have encryption turned on and preferably MDM must be installed. Basic device security and access policies must be used (encryption, authentication, complex passwords, etc.).”
Gary DeMercurio, Red Team Director at Coalfire:
“Everything can be breached with enough force. In terms of what happened at The Capitol, outside of building a giant concrete wall with a single point of entry, not much else would have stopped a mob of that size. Having the computer system on a separate circuit that could have been shut down in the event of a breach would have prevented a lot of this. (physical issues such as keyloggers would have still existed as well as laptops left unlocked under their own power) Severing the network connection of all computers would have helped as well.
Corporations should integrate constant offensive testing to ensure both the physical and logical security measure that are in place, actually work. Too often companies abide by the same “security” taught and passed down from predecessors and outdated training method and overlook testing of those protocols they have in place. Working from home has expanded that attack surface, it has also weakened the corporate security tremendously. Just as they reported on the news during the recent Capitol Hill incident, “We were lucky the building was so empty due to COVID-19”. How many empty building are there now? How hard is it to walk into an empty building and sit down at a desk and run roughshod on the corporation? With what happened in Washington DC, this is more about emergency response, and cleaning up the mess as it can happen to anyone. Corporations should ensure they have a procedure for what happens if and when it finally happens to them.”
Jack Mannino, CEO at nVisium:
“If you’re concerned that your employees will have to rapidly abandon their workstations in the event of a crisis, there are steps you can take to reduce your exposure. First, consider using proximity based authentication solutions or physical tokens, where a workstation would quickly lock even if a user didn’t have time to manually do it themselves. Ensure all drives are encrypted at-rest to prevent unauthorized access to stored information. Utilize remote administration and data wiping solutions that would enable you to regain control of a device in the event you could not physically access it.”
Tom Pendergast, Chief Learning Officer at MediaPro:
“The answer is not dissimilar to how we prepare organizations to respond to external cyberattacks like phishing: we build tons of good technical defenses, then we train people how to respond to the rare phishing attempt that gets through—knowing that relying on individuals who are focused on other things to resist attack is an imperfect defense. Yesterday, at a critical moment, it’s as if we turned all the technical defenses off and allowed the threat to overrun the environment. Nobody was ready for that! I’m sure some people responded appropriately—but clearly, many did not.
In the end, this situation required a bunch of individuals to take specific actions (lock the workstation, gather mobile devices, secure paper) during a highly stressful time—and the only way I know of to ensure high performance in such a situation is to practice, practice, practice. But allotting time to practice requires a systemic acknowledgment of risk (which was not present yesterday but may be in the future) and then an organizational commitment to focus on building the skills to reduce that risk (again, likely not present yesterday in the organization). The easier solution in this case will likely be to reduce the chances that such an assault will occur again, for that is easier than preparing the individual employees.”












