The DDoS threat is increasing again. Pbot can generate 75 Gbps from just 400 nodes and Mirai has been commoditized. However, despite the growing number of attacks, the overall trend seems to be for more frequent, smaller attacks. These are the primary takeaways from a new Q2 study into internet traffic.
Akamai Technologies, a Cambridge, Mass.-based content delivery network (CDN) and cloud services provider with more than 233,000 servers in over 130 countries, has published its Q2 State of the Internet report (PDF). The report comprises analyses of attack data seen across this network. It shows that DDoS attacks have increased by a massive 28% over the previous quarter.
Within this statistic, infrastructure layer (layers 3 and 4) attacks have risen by 27%; reflection-based attacks have risen 21%; and the average number of attacks per target has increased by 28%. Gaming sites are frequent targets, accounting for 81% of all volumetric DDoS attacks monitored by Akamai.
While the average number of attacks per target rose to 32 over the period, one gaming site suffered 558 attacks, averaging six per day throughout the period.
The final months of 2016 were notable for the largest DDoS attacks ever seen; but the current trend, suggests the report, is for smaller attacks. This is despite the continued availability of the Mirai botnet, and the use of Pbot malware to create mini-DDoS botnets able to generate a 75 Gbps attack from just 400 bots. Pbot’s power comes from infecting webservers able to create more traffic per node than, say, Mirai’s infection of large numbers of small IoT devices.
“We know that massive DDoS attacks are possible,” says the report, “but could this be a new trend going forward? Have DDoS attackers taken to more subtle, targeted attacks to avoid drawing attention?”
This possibility is given extra weight by the evolving nature of Mirai attacks. Akamai was one of the first Mirai targets in Fall 2016, and has continued to be a target. This long-standing adversarial relationship has allowed Akamai to study Mirai in some depth.
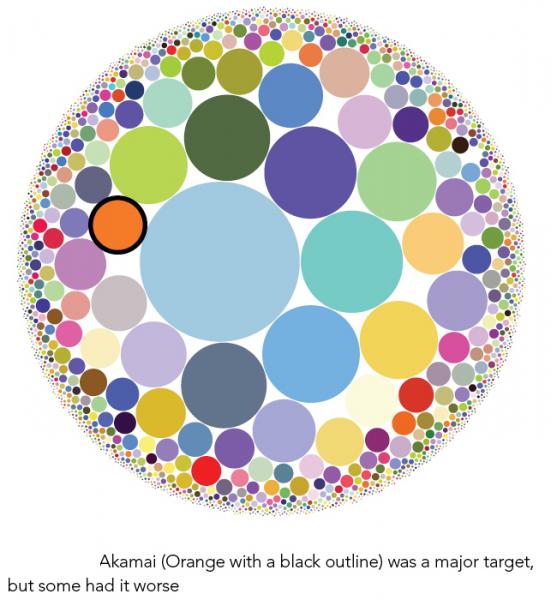
Mirai is often thought of as a single massive network of bots. In reality, says Akamai, “it is more akin to smaller hives of related bots and C&Cs.” An analysis of different Mirai C&Cs shows that parts of Mirai are used to attack different targets, with some C&Cs attacking multiple targets, and others attacking a single target.
“At least one botnet operator was offering access to the systems under its control for rent,” notes Akamai, “which may explain why some botnets attacked such a large number of IP addresses.”
Akamai says it will continue its research into and analysis of Mirai, but for now notes that it appears to be contributing to the commoditization of DDoS. The large number of different attacks emanating from single C&Cs can be considered as ‘pay-for-play’ attacks — they were seen attacking IPs for a short duration, going inactive, and then re-emerging to attack different targets.
The report also notes that DNS traffic analysis can be used to passively locate the likely incidence of malware infections. Ever since Conficker, malware has been using domain generation algorithms (DGAs) to hide their C&C infrastructure. These DGAs generate many pseudo-random IP addresses every day. The attacker needs to choose only one of the expected domains and register it ‘just in time’, and then abandon it after use. The malware, however, doesn’t know which is the correct IP to contact, and cycles through the possibilities until it finds the right one.
Akamai analyzed the traffic of more than 2.5 million connected networks. One hundred and forty were known to be infected with malware. “When looking at the average number of unique domains accessed per hour,” notes the study, “we saw that infected networks had approximately 15 times the lookup rate of a clean network.” This is explained by the malware trying to access the DGA-generated IPs. “Since most of the generated domains were not registered, trying to access all of them created a lot of noise.”
DNS monitoring is thus a potential method of breach detection. “Security defenders are advised to make certain they are using a combination of security monitoring products that include DNS monitoring,” concludes Akamai. “Having visibility into different areas of the enterprise network will increase detection and reduce risks. For the best defense, security controls should also be in place on endpoint devices and the inner network, not just Internet connectivity.”
Related: Pulse Wave DDoS Attacks Disrupt Hybrid Defenses
Related: North Korea’s DDoS Attacks Analyzed Based on IPs
Related: Don’t Be In Denial About DDoS













