Montenegro has been targeted in a disruptive cyberattack blamed on Russian hackers, and a known ransomware group may have been involved.
The country’s Agency for National Security announced last week that government servers had been targeted in an ongoing attack that was described as massive and coordinated.
The attack targeted government systems and other critical infrastructure, and managed to cause some disruptions. The US embassy warned citizens residing in the country that the attack could disrupt transportation, public utilities and telecommunications.
However, officials in Montenegro said no data was stolen during the attack and claimed that no permanent damage was done. Authorities said the attack was politically motivated and launched by multiple Russian agencies.
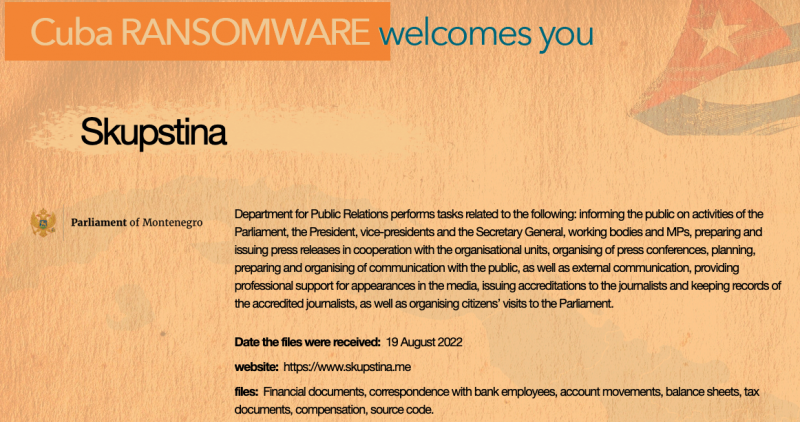
After Montenegro announced the incident, the ransomware group called Cuba said on its Tor-based leak website that it breached systems of the country’s parliament.
The cybercriminals claim to have stolen files on August 19, including financial documents and source code. They allegedly obtained correspondence with bank employees, balance sheets, account activity, compensation data, and tax documents.
The Cuba ransomware page dedicated to the Parliament of Montenegro has a download button that should presumably allow users to obtain the stolen files, but the download does not appear to work at the time of writing.
The Cuba ransomware has been around since 2019 and last year the FBI issued an alert to warn organizations that the cybercriminals had been targeting critical infrastructure. The FBI had been aware of roughly 50 targeted entities and the agency said the hackers received tens of millions of dollars from victims.
The threat actor encrypts files on compromised systems and also steals information from victims in an effort to increase its chances of getting paid.
An analysis conducted last year by SecurityJoes and Profero showed that Cuba ransomware operators are likely Russian speakers. The Russian government has been accused of shielding — and sometimes even employing — cybercriminals.
This would not be the first time a ransomware group has targeted a government. In May, the threat actor behind the notorious Conti ransomware targeted Costa Rica’s computer systems and threatened to overthrow the government. Experts believe this was part of an effort to make a grand exit — the Conti operation was shut down shortly after, likely due to the brand becoming toxic.
In addition, the LockBit group claimed earlier this year that it had breached the systems of France’s Ministry of Justice.
Related: US Government Shares Photo of Alleged Conti Ransomware Associate
Related: Black Basta Ransomware Becomes Major Threat in Two Months
Related: LockBit Ransomware Site Hit by DDoS Attack as Hackers Start Leaking Entrust Data

