The days when the Black Hat USA and Defcon conferences are ongoing are two times when surfing the Internet in Las Vegas can be a gamble all on its own.
According to Imperva, there was a spike in malicious activity emanating from Sin City two weeks ago when the conferences were under way.
“I decided to test for attack traffic originating in Las Vegas during BlackHat and Defcon, and a month prior to that in order to correlate to baseline,” blogged Barry Shteiman, Imperva’s director of security strategy. “In order to do that, we collected all of the security events during that time period from our Community Defense system, mapped Geo IPs for Nevada state, and Las Vegas specifically, then we queried the Community Defense data set for all source IPs that were in the US. Finally, we summarized by date and where the city itself is Las Vegas.”
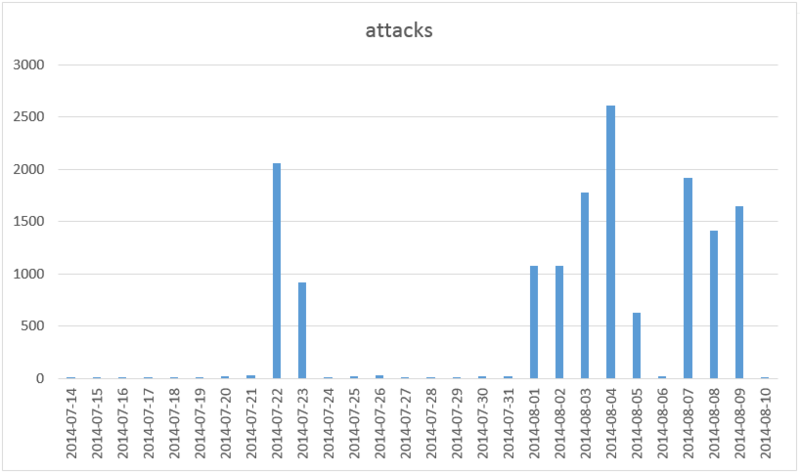
Here’s what the company found. Typically, it detects roughly 20 attacks originating from Las Vegas on a normal day. However, during the conferences that number peaked at 2,612. There was a significant drop off as Black Hat began winding down. On Aug. 6, the conference’s second to last day, there were just 20 detected attacks. The start of Defcon – which is also the final day of Black Hat – erased that decline however and the number of attacks shot back up to 1,916 on Aug. 7.
On the final day of Defcon, Aug. 10, the number of detected attacks fell to 7.
Imperva also noted a jump in attack volume during the NAACP conference in July, which indicates one of a few possibilities: either a large crowd in a conference-scale event causes a growth in attack volume due to malware on computers, or attackers are attending the conference and performing their attacks from there, Shteiman wrote. As for Black Hat and Defcon, they are not exactly typical conferences, he added.
“They have some of the brightest security/hacking minds in the world attending,” he blogged. “Those guys who read every link before they click, run custom operating systems in cases and are generally very aware to security and therefore are less likely to be drive-by victims of hacking – for that reason, seeing numbers that high is more substantial at a hacker conference than in other conferences.”















