Cyber-criminals are employing new tactics to circumvent the risk analytics engines used by banks to detect financial fraud, Trusteer researchers found.
![]() Criminals intercept a complete set of login credentials, block legitimate users from accessing the account, and log into a compromised account before the one-time password expires, Amit Klein, Trusteer’s CTO, wrote on the Trusteer blog. By tricking users into entering the one-time password and blocking login attempts to the site, criminals circumvent the risk analytics tools used by banks to detect fraudulent behavior.
Criminals intercept a complete set of login credentials, block legitimate users from accessing the account, and log into a compromised account before the one-time password expires, Amit Klein, Trusteer’s CTO, wrote on the Trusteer blog. By tricking users into entering the one-time password and blocking login attempts to the site, criminals circumvent the risk analytics tools used by banks to detect fraudulent behavior.
Banks rely on risk engines to detect cases where user credentials may have been stolen. The engines identify theft by looking for multiple devices simultaneously logged into a single account and successive logins from locations that are geographically too far apart. Either of these incidents indicate fraud is being attempted and give banks time to take action, Klein wrote.
“However, because fraudsters tend to be a persistent and innovative bunch, they have developed new approaches to circumvent these detection techniques,” Klein wrote.
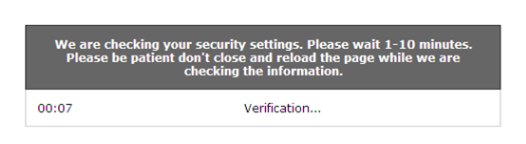
Klein outlined a scenario in which a user’s computer or device was infected with malware capable of intercepting user credentials, such as Zeus or SpyEye. When the user tried to login to a banking site, the malware harvested the username, password and one-time password and transferred the information to a remote command-and-control server. The user is then shown a page claiming the online banking site is temporarily down.
Multiple login attempts from different locations is a clear indicator of real-time credential theft, Klein wrote. However, since the login request never reached the bank’s servers, so there was no record of the legitimate user’s login attempt. As far as the bank’s risk assessment engine was concerned, the user happened to be logging in from an unknown device from a different location for the first time.
Many banking sites prompt users to enter one-time password if logging in from an unknown device. In this case, the user was tricked by the malware into handing the information over despite being on a recognized device. Since the criminals are logging in near-real-time, the password had not yet expired.
Since the user is not logged in, and the bank doesn’t know about the initial login attempt, the fraudulent transaction doesn’t trigger any alarms over at the bank, Klein wrote.
Using session blocking man-in-the-browser attacks increase the criminals chances of avoiding detection by the risk assessment tools and successfully committing fraud, Klein said.















