A stored cross-site scripting (XSS) vulnerability found in a popular comments widget exposed a large number of websites to attacks. The security hole was quickly patched by the product’s developers.
A 14-year-old security enthusiast named Ibram Marzouk recently discovered a stored XSS flaw in the comments section of code snippet marketplace PasteCoin.
A friend of Marzouk’s, Karim Rahal, who is also 14, later noticed that the XSS vulnerability was not limited to PasteCoin and instead affected HTML Comment Box, a popular widget that allows web designers and developers to add a simple comment box to their websites.
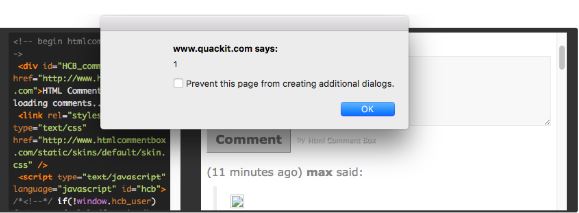
HTML Comment Box is designed to filter user input in an effort to prevent XSS attacks, but the payload used by Rahal bypassed the filter: “>><<img src=x onerror=alert(1);//>>
“The open and closing tags filter was bypassed using double ‘greater than (>)’ and ‘lower than (<)’ tags. In addition, the filter that checks the attributes used was bypassed by closing the attribute with a ‘semicolon (;)’ and the double ‘slashes (//)’ would comment out the javascript,” Rahal explained in a post on Detectify’s blog.
The vulnerability was reported to the developer of HTML Comment Box through Detectify’s recently launched crowdsourced bug bounty program. The developer patched the flaw within a couple of hours.
A Google search conducted by Rahal returned roughly 2 million pages that had been using the comments widget. The same search performed by SecurityWeek returned more than 760,000 results, including many duplicates. Nevertheless, it’s clear that HTML Comment Box is present on many sites.
This is not the first time researchers have found vulnerabilities in the comments widget. Back in 2013, researchers Rafay Baloch and Deepankar Arora identified both persistent and reflected XSS flaws in HTML Comment Box.
Related Reading: Google Releases New XSS Prevention Tools
Related Reading: XSS Flaws Decline, DoS Becomes More Common
Related Reading: WordPress Flaw Allows XSS Attack via Image Filenames













