Researchers at cybersecurity firm Trend Micro have shown that the computer numerical control (CNC) machines present in many modern manufacturing facilities are vulnerable to hacker attacks.
Trend Micro is presenting the research this week at SecurityWeek’s 2022 ICS Cyber Security Conference in Atlanta, which can also be joined online via SecurityWeek’s virtual event platform. Registration for the event is still open.
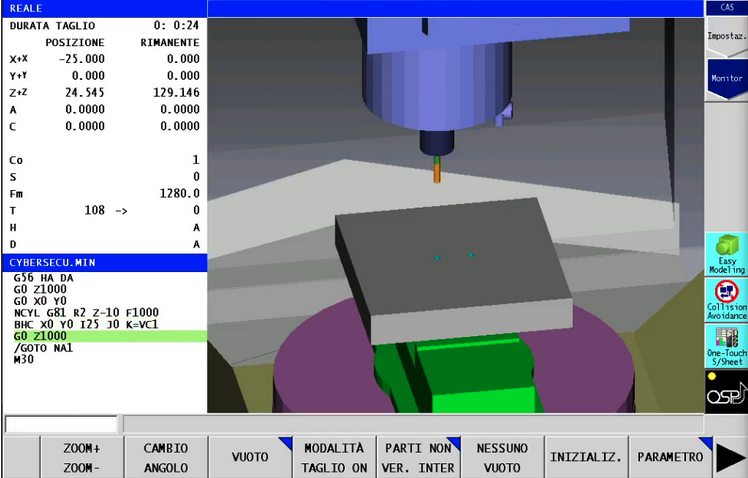
CNC machines can be programmed to carry out a wide range of tasks with a high level of efficiency, consistency and accuracy. They include mills, lathes, plasma cutters, electric discharge machines, water jet cutters, and punch presses.
CNC machines are increasingly complex, enabling users to operate them remotely and extend their functionality by installing add-ins. This increasing complexity means they can be increasingly vulnerable to cyberattacks.
Trend Micro researchers have analyzed CNC products from Haas, Okuma, Heidenhain and Fanuc, which are used by manufacturing organizations worldwide. The analysis showed that the machines provided by each of these vendors are vulnerable to roughly a dozen types of attacks.
The researchers demonstrated that an attacker could cause damage or disruption, they can hijack a machine, or steal valuable intellectual property. Each of these scenarios could have a significant financial impact on an organization.
For instance, a hacker could cause damage or disruption to a CNC machine or the item the machine is working on by altering some of the device’s geometry or the controller’s program. The attacker can cause visible damage, or they can make minor changes that result in a defective product.

Hackers could also disrupt the manufacturing process by triggering alarms that cause the machine to stop operating until a human intervenes. These alarms are designed to stop the machine in case of software or hardware faults, but an attacker could also trigger an alarm.
A threat actor who has access to the CNC machine and its associated systems could launch ransomware attacks, where files are encrypted or legitimate users are prevented from accessing the user interface.
Another risk is related to data theft. These machines are often tasked with making parts for which the design can be highly valuable. An attacker could steal the program run by the targeted machine and then easily reverse engineer it to obtain the code.
In addition, CNC controllers can store valuable information related to production, which can also be useful to threat actors specializing in corporate espionage.
These types of attacks can be prevented, Trend Micro says, by using industrial intrusion detection and prevention systems, segmenting networks, correctly configuring CNC machines, and ensuring that they are always up to date.
The cybersecurity firm started notifying impacted CNC vendors last year and says they have all taken steps to reduce the risk of malicious attacks, including through patches and new security features.
Related: Realistic Factory Honeypot Shows Threats Faced by Industrial Organizations
Related: Vulnerabilities in Protocol Gateways Can Facilitate Attacks on Industrial Systems
Related: Legacy Programming Languages Pose Serious Risks to Industrial Robots
Related: Old RF Protocols Expose Cranes to Remote Hacker Attacks

