A significant number of Cisco switches located in Iran and Russia have been hijacked in what appears to be a hacktivist campaign conducted in protest of election-related hacking. However, it’s uncertain if the attacks involve a recently disclosed vulnerability or simply abuse a method that has been known for more than a year.
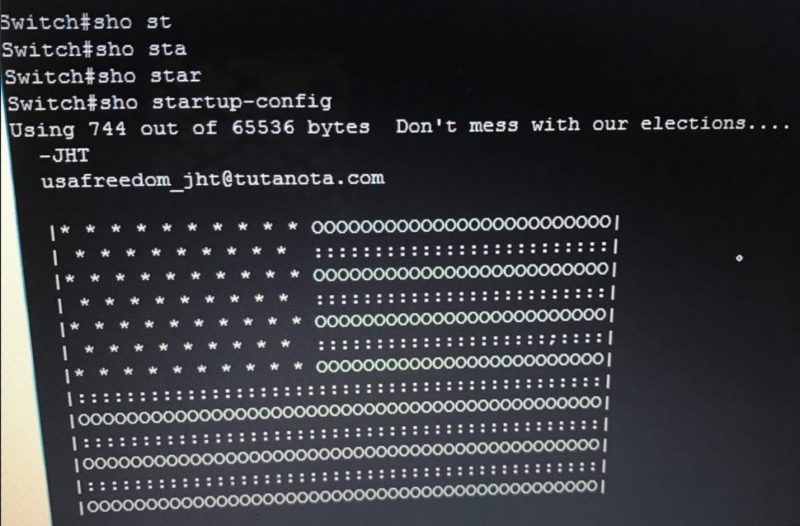
Cisco devices belonging to organizations in Russia and Iran have been hijacked via their Smart Install feature. The compromised switches had their IOS image rewritten and their configuration changed to display a U.S. flag using ASCII art and the message “Don’t mess with our elections…”
The hackers, calling themselves “JHT,” told Motherboard that they wanted to send a message to government-backed hackers targeting “the United States and other countries.” They claim to have only caused damage to devices in Iran and Russia, while allegedly patching most devices found in countries such as the U.S. and U.K.
Iran’s Communication and Information Technology Ministry stated that the attack had impacted roughly 3,500 switches in the country, but said a vast majority were quickly restored.
Kaspersky Lab reported that the attack appeared to mostly target the “Russian-speaking segment of the Internet.”
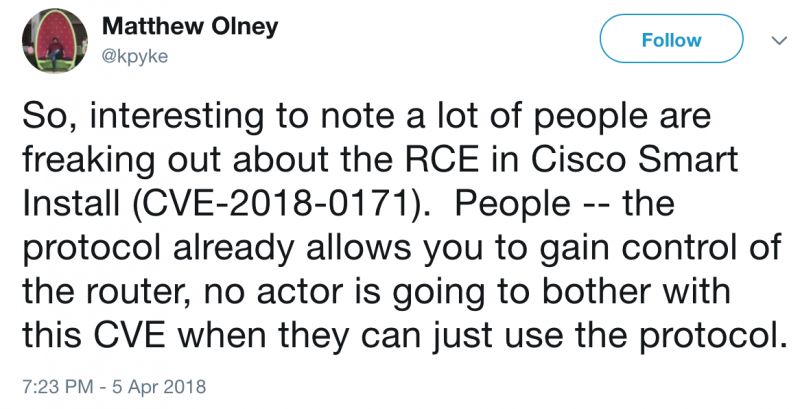
While there are some reports that the attack involves a recently patched remote code execution vulnerability in Cisco’s IOS operating system (CVE-2018-0171), that might not necessarily be the case.
The Cisco Smart Install Client is a legacy utility that allows no-touch installation of new Cisco switches. Roughly one year ago, the company warned customers about misuse of the Smart Install protocol following a spike in Internet scans attempting to detect unprotected devices that had this feature enabled.
Attacks, including ones launched by nation-state threat actors such as the Russia-linked Dragonfly, abused the fact that many organizations had failed to securely configure their switches, rather than an actual vulnerability.
Cisco issued a new warning last week as the disclosure of CVE-2018-0171 increases the risk of attacks, but the networking giant said it had not actually seen any attempts to exploit this vulnerability in the wild. Cisco’s advisory for this flaw still says there is no evidence of malicious exploitation.
There are hundreds of thousands of Cisco switches that can be hijacked by abusing the Smart Install protocol, and Cisco Talos experts believe attackers are unlikely to bother using CVE-2018-0171.
The Network Security Research Lab at Chinese security firm Qihoo 360 says the data from its honeypot shows that the attacks have “nothing to do with CVE-2018-0171” and instead rely on a publicly available Smart Install exploitation tool released several months ago.
While none of the major players in the infosec industry have confirmed that the attacks on Iran and Russia rely on CVE-2018-0171, technical details and proof-of-concept (PoC) code have been made available by researchers, making it easier for hackers to exploit.
Hamed Khoramyar, founder of Sweden-based ICT firm Aivivid, said the attacks exploited CVE-2018-0171. Kudelski Security also reported seeing attacks involving both CVE-2018-0171 and another recently disclosed IOS vulnerability tracked as CVE-2018-0156. However, Kudelski’s blog post also lists Khoramyar as one of its sources.

