Cisco has advised organizations to ensure that their switches cannot be hacked via the Smart Install protocol. The networking giant has identified hundreds of thousands of exposed devices and warned that critical infrastructure could be at risk.
The Cisco Smart Install Client is a legacy utility that allows no-touch installation of new Cisco switches. Roughly one year ago, the company warned customers about misuse of the Smart Install protocol following a spike in Internet scans attempting to detect unprotected devices that had this feature enabled. It also made available an open source tool for identifying devices that use the protocol.
Attackers can abuse the Smart Install protocol to modify the configuration file on switches running IOS and IOS XE software, force the device to reload, load a new IOS image, and execute high-privilege commands. These attacks rely on the fact that many organizations fail to securely configure their switches, rather than an actual vulnerability.
According to Cisco, sophisticated nation-state groups have also abused Smart Install in their campaigns, including the Russia-linked threat actor tracked as Dragonfly, Crouching Yeti and Energetic Bear, which has been known to target critical infrastructure.
Cisco has decided to once again warn organizations of the risks associated with Smart Install following the disclosure of a critical vulnerability discovered recently by researchers at Embedi.
The flaw, tracked as CVE-2018-0171, allows a remote and unauthenticated attacker to cause a denial-of-service (DoS) condition or execute arbitrary code by sending specially crafted Smart Install messages to an affected device on TCP port 4786. Researchers said they had identified roughly 250,000 vulnerable Cisco devices with TCP port 4786 open.
Cisco’s own Internet scans revealed 168,000 systems potentially exposed due to their use of the Cisco Smart Install Client. The company says the number of impacted devices has decreased considerably since 2016, when security firm Tenable identified more than 250,000 exposed systems.
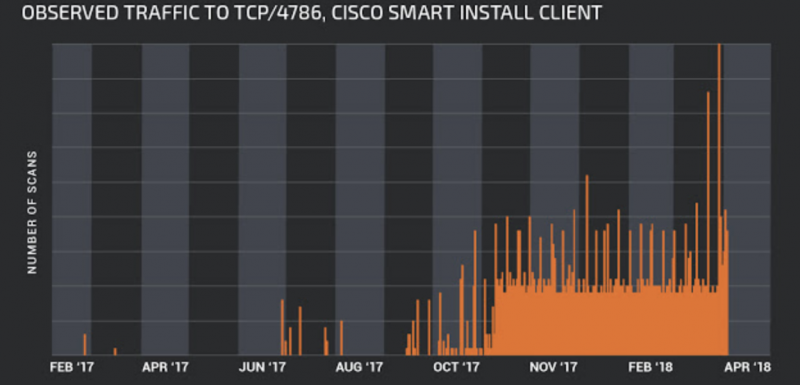
Throughout the end of 2017 and early 2018, Cisco’s Talos group noticed attackers increasingly looking for misconfigured clients. Now that CVE-2018-0171 has been found, the risk of attacks has increased even more, especially since Embedi has released technical details and proof-of-concept (PoC) code.
There is no evidence that CVE-2018-0171 has been exploited in malicious attacks. Cisco also noted that much of the activity it has seen is likely not malicious, but the company says the sharp increase in scanning is noteworthy.
The vendor has provided recommendations for preventing potential attacks and advised customers to remove the Smart Install Client from devices where it’s not needed. Smart Install is enabled by default on switches that have not received a recent update that automatically disables the feature when it’s not in use.
While it’s unclear if Smart Install was involved, Cylance reported recently that the Dragonfly cyberespionage group had hijacked a core Cisco router at a major state-owned energy conglomerate in Vietnam and abused it to obtain credentials that were later leveraged in attacks targeting energy companies in the United Kingdom.
Related: US Accuses Russian Government of Hacking Infrastructure
Related: DHS, FBI Warn of Ongoing APT Attack Against Critical Infrastructure











