At the Virus Bulletin Conference last week, two security researchers explained how they were able to compromise the command and control (C&C) panels of 10 Internet of Things (IoT) botnets.
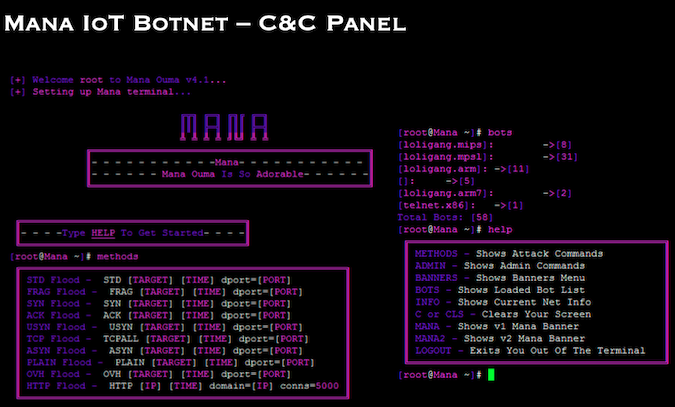
The researchers, Aditya K. Sood and Rohit Bansal of SecNiche Security Labs, revealed at the online conference that they were able to access the C&C panels of the Mana, Vivid, Kawaii, Verizon, Goon, 911-Net, Purge Net, Direct, 0xSec, and Dark botnets.
According to Sood and Bansal, possible approaches to such compromise would first involve mapping the remote servers that are distributing binaries, or extracting the binaries dropped onto compromised IoT devices, and then extracting the hardcoded IP addresses from these files, to learn where those panels are located.
However, it is also possible to extract artefacts from network traffic, including IP addresses, or even extract C&C information from malicious processes running on the compromised devices (effective if the address is generated on the fly).
One other approach involves mass scanning the Internet for potentially suspicious IoT devices, finding exposed administrative interfaces and attempting to compromise them to extract information on C&C servers. Scanning for remote servers based on known indicators is also possible.
The next step after identifying the attacker’s server is accessing the C&C panel, which can be done through the frontend admin interface by brute-forcing credentials. Access can also be obtained by compromising a backend database to gain access to administrative credentials, finding and exploiting vulnerabilities in the C&C panel, or using cracked credentials, the researchers said.
In the event that the C&C interface cannot be breached, one could also attempt to crash the server, or kill it. By analyzing the source code of botnet malware, such as that for Mirai, which is available online, one could identify the buffer allocation for various functions, discover vulnerable ones to trigger overflows, craft a buffer and then send it to the target to see if the crash happens.
At the VB 2020 conference, the two researchers revealed that they used these approaches to access the C&C panels of the aforementioned IoT botnets, which then allowed them to learn more about the capabilities of these threats and the manner in which they are operated.
They obtained information on the commands supported by the botnets, the various options available for administrators, including those employed for launching distributed denial of service (DDoS) or similar attacks, as well as the similarities and differences between the different panels.
The two researchers also detailed specific techniques which, they say, could be used to create additional attack scenarios, not only to hack back at IoT botnets, but also to build defensive measures against them.
In fact, they argue, compromising these C&C panels is highly important for gathering threat intelligence and building defenses against IoT botnets, pointing out that otherwise it would be difficult to understand how exactly the botnets operate.
Related: Black Hat Wrap-Up: IoT and Hardware Vulnerabilities Take the Spotlight
Related: Botnet Targets Critical Vulnerability in Grandstream Appliance
Related: New ‘Kaiji’ Botnet Attacks Linux, IoT Devices via SSH Brute Force

