Organizations are getting increasingly better at discovering data breaches on their own, with more than 60% of intrusions in 2017 detected internally, according to FireEye-owned Mandiant.
The company’s M-Trends report for 2018 shows that the global median time for internal detection dropped to 57.5 days in 2017, compared to 80 days in the previous year. Of the total number of breaches investigated by Mandiant last year, 62% were discovered internally, up from 53% in 2016.
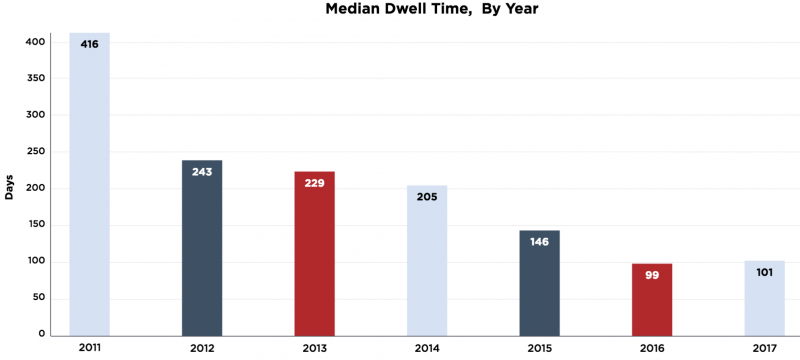
On the other hand, it still took roughly the same amount of time for organizations to learn that their systems had been compromised. The global median dwell time in 2017 – the median time from the first evidence of a hack to detection – was 101 days, compared to 99 days in 2016.
Companies in the Americas had the shortest median dwell time (75.5 days), while organizations in the APAC region had the longest dwell time (nearly 500 days).
Data collected by Mandiant in 2013 showed that more than one-third of organizations had been attacked again after the initial incident had been remediated. More recent data, specifically from the past 19 months, showed that 56% of Mandiant customers were targeted again by either the same group or one with similar motivation.
In cases where investigators discovered at least one type of significant activity (e.g. compromised accounts, data theft, lateral movement), the targeted organization was successfully attacked again within one year. Organizations that experienced more than one type of significant activity were attacked by more than one threat actor.
Again, the highest percentage of companies attacked multiple times and by multiple threat groups was in the APAC region – more than double compared to the Americas and the EMEA region.
When it comes to the most targeted industries, companies in the financial and high-tech sectors recorded the highest number of significant attacks, while the high-tech, telecommunications and education sectors were hit by the highest number of different hacker groups.
Last year, FireEye assigned names to four state-sponsored threat groups, including the Vietnam-linked APT32 (OceanLotus), and the Iran-linked APT33, APT34 (OilRig), and APT35 (NewsBeef, Newscaster and Charming Kitten).
“Iran-sponsored threat actors have compromised a variety of organizations, but recently they have expanded their efforts in a way that previously seemed beyond their grasp,” Mandiant said in its report. “Today they leverage strategic web compromises (SWC) to ensnare more victims, and concurrently maintain persistence across multiple organizations for months and sometimes years. Rather than relying on publicly available malware and utilities, they develop and deploy custom malware. When they are not carrying out destructive attacks against their targets, they are conducting espionage and stealing data like professionals.”
Related: Organizations Getting Better at Detecting Breaches
Related: Financial Attackers as Sophisticated as Nation-State Groups













