Hackers continue to exploit the recently patched BIG-IP security flaw and they have plenty of potential targets as researchers have identified thousands of vulnerable systems.
The vulnerability affecting F5 Networks’ BIG-IP application delivery controller (ADC) is tracked as CVE-2020-5902 and it was disclosed last week by the vendor and Positive Technologies, the cybersecurity company whose researchers identified the issue. F5 has released patches and organizations have been advised to apply them immediately.
The security hole has been described as a critical remote code execution vulnerability that can be exploited to take complete control of a system. The issue is related to the Traffic Management User Interface (TMUI) configuration utility. An attacker who has access to this utility can exploit the weakness to create or delete files, disable services, intercept data, and run arbitrary code or commands.
While there are roughly 8,000 BIG-IP servers exposed to the internet, threat intelligence company Bad Packets has determined that roughly 3,000 of them are vulnerable to attacks exploiting CVE-2020-5902. A majority are in the United States (1,200), followed by China (500), Taiwan (140), and several other Asian countries.
According to Bad Packets, there are 635 unique network providers hosting vulnerable BIG-IP endpoints, including government organizations, educational institutions, healthcare providers, financial institutions, and Fortune 500 companies.
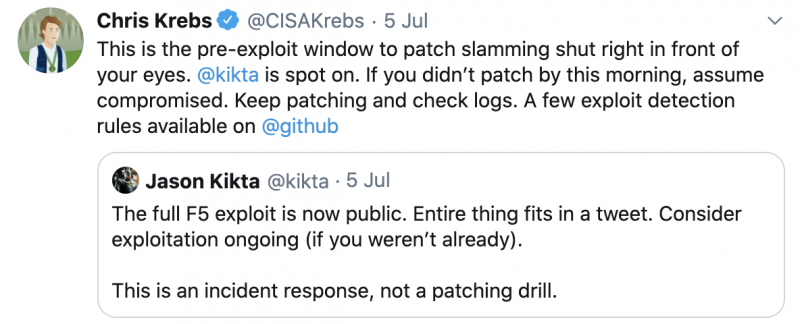
Proof-of-concept (PoC) exploits and technical information were made public for CVE-2020-5902 shortly after its disclosure and the first exploitation attempts were observed soon after. The vulnerability is easy to exploit and experts have pointed out that the entire exploit fits in a tweet.
Hackers have been scanning for vulnerable systems, and some of the exploits attempted to obtain passwords from vulnerable devices. Bad Packets reported on Monday that it has also seen a piece of DDoS malware being delivered via CVE-2020-5902 from an IP address known to have been involved in malicious activities.
Chris Krebs, the director of the U.S. Cybersecurity and Infrastructure Security Agency (CISA), told organizations to assume that their systems have been compromised if the patch was not immediately installed.
Related: “Ticketbleed” Flaw Exposes F5 Appliances to Remote Attacks
Related: Flaw in F5 Products Allows Recovery of Encrypted Data
Related: Hidden Injection Flaws Found in BIG-IP Load Balancers














