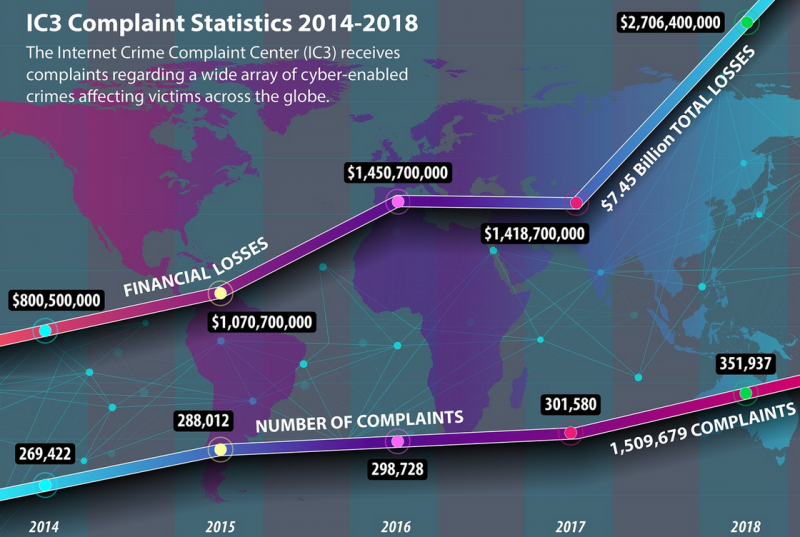
The 2018 Internet Crime Report (ICR) shows that both the incidence and cost of internet crime continues to escalate. Complaints rose 14.3% from 2017 to 351,937 in 2018. Associated losses increased by 90.8% from $1,418.7 million to $2,706.4 million over the same period.
The Internet Crime Report is an annual report compiled by the FBI’s Internet Crime Complaint Center (IC3). IC3 provides an online reporting point for victims of internet crime. It has developed into a repository for details on internet crime, and a database of details and statistics available to U.S. law enforcement agencies.
The latest ICR was published on April 22, 2019. While everybody is a target for internet crime, the report shows more victims and greater losses occurred in the over-60 age bracket. 62,085 over-60 victims lost just under $650 million compared to 48,642 victims aged 50-59 losing just under $495 million.
The single most reported crime was the non-payment/non-delivery scam. Non-payment occurs when goods are shipped, but the recipient denies receipt and refuses to pay. Non-delivery is when goods are paid for, but never shipped. During 2018, IC3 received complaints from 65,116 victims with associated losses of $183,826,809.
However, the greatest financial loss to internet crime came from business email compromise (BEC) and email account compromise (EAC) scams. Here, 20,373 victims lost a total of $1.298 billion. BEC scams target businesses working with foreign suppliers or regularly performing wire transfer payments. EAC is similar, but targets individuals.
BEC frauds began to be popular in 2013. A that time they were known as ‘fake president’ or ‘fake CEO’ frauds. At that time, CEOs and chief financial officers were the usual target. It is carried out by first compromising legitimate business email accounts in order to issue false instructions or request to wire funds to an account controlled by the attacker.
“BEC and EAC are constantly evolving as scammers become more sophisticated,” notes the report. “Through the years, the scam has seen personal emails compromised, vendor emails compromised, spoofed lawyer email accounts, requests for W-2 information, and the targeting of the real estate sector.”
The latest variation on this theme, which increased during 2018, was BEC scams spoofing a person in authority and requesting the recipient to purchase multiple gift cards for either personal or business reasons.
To combat the growth in BEC/EAC financial fraud, IC3 introduced its Recovery Asset Team (RAT) in February 2018. Its purpose is to streamline communications with financial institutions in order to block and recover transfers to U.S. accounts made under fraudulent pretenses.
Between February 2, 2018, and December 31, 2018, the RAT got involved with 1,061 such domestic scams. These scams incurred a total loss to the victims of $257.1 million; but the RAT recovered $192.7 million — a recovery rate of 75%.
In an early example in February 2018, the IC3 RAT received a complaint filed by a BEC victim in New York. This involved the closing of a real estate transaction, where a compromised email account requested the transfer of $50,000 to a fraudulent bank account also in New York. The RAT contacted the bank’s fraud department; and IC3, the victim and the bank worked together. The funds were returned to the victim in full.
After BEC/EAC, the next most-costly internet crime is Confidence Fraud/Romance, where 18,493 victims reported losses of $362,500,761. In some ways, this is an old-fashioned confidence trick. A perpetrator convinces the victim that a special trust relationship exists between them, and persuades the victim to send money or financial information, or to launder money.
The second most popular crime in 2018 was extortion. Here, 51,146 victims lost a total of $83,357,901 to the criminals. This represents a 242% increase in extortion related complaints from 2017. The usual method is for the criminal to threaten physical or financial harm, or the release of sensitive or incriminating data.
On February 7, 2018, IC3 referred a combined extortion and DDoS threat to the Los Angeles Field Office. A consequent investigation determined that the email threat had an affiliation to the Apophis Squad — a group that had been reported for multiple bomb threats to schools, and DDoS extortion threats to companies.
Throughout the year, IC3 provided more Apophis-related information, and one year later, on February 8, 2019, Timothy Dalton Vaughn and George Duke-Cohan were federally indicted.
It is worth noting that these are not national crime statistics, but just statistics from internet crimes reported to IC3. True figures will almost certainly be higher. One example would be ransomware, where IC3 figures show a total of $3,621,857 lost to 1,493 victims. This figure does not include any remediation costs, nor can it account for incidents where the victim simply pays the ransom without reporting the crime. The true cost of ransomware will be much higher.
Related: Man Pleads Guilty Over $100M BEC Scheme Targeting Google, Facebook
Related: Nigerian Hackers Attempt to Steal Millions From Shipping Firms
Related: FBI: $1.45 Billion in Losses to Internet Crime Reported in 2016















