Human rights watchdog Amnesty International has uncovered a sophisticated phishing campaign targeting journalists, activists and other entities in Nepal and Qatar interested in migrants’ rights.
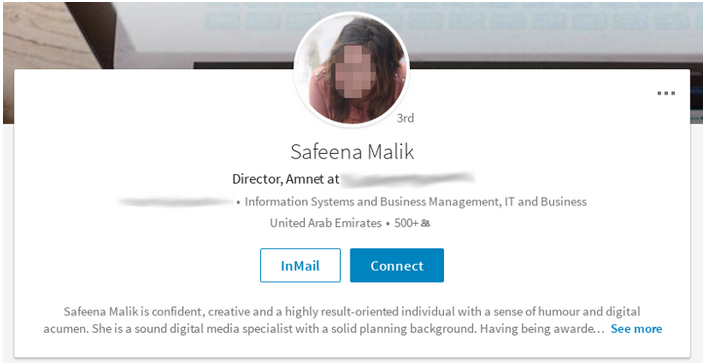
The campaign, dubbed Operation Kingphish, involves an online persona named “Safeena Malik” – Malik can mean “king” in Arabic. Amnesty International learned that Safeena Malik had contacted several individuals via email and social media over the course of 2016.
Safeena Malik, who claimed to be an activist interested in human rights, had accounts on several social media websites, including Twitter, Facebook and LinkedIn. “She” reached out to dozens of people, many involved in the issue of migrants’ rights in Qatar.
Qatar has attracted the attention of several human and labor rights organizations for its exploitation of migrant workers, many of which are from Nepal. Some of the documented cases are related to the construction of stadiums and infrastructure for the FIFA World Cup competition that will be hosted by Qatar in 2022.
According to Amnesty, many of the attacks launched using the fake Safeena Malik profiles attempted to lure targeted individuals to realistic Google phishing pages. In order to avoid raising suspicion, the phishing pages displayed the email address and profile picture of the targeted user, and a legitimate document was displayed once the password had been handed over to the attacker.
Documents on human trafficking and ISIS funding, and fake Google Hangouts invitations were used to lure targeted users to the phishing pages. Safeena Malik also sent out private messages on Facebook to obtain the Gmail addresses of the targets.
The persona had hundreds of connections on social media and often joined groups focusing on migrant workers and forced labor in an effort to identify potential targets and make it appear as if “she” was part of the community.
Amnesty identified 30 different targets by analyzing the profile pictures hosted on the server used by the attacker to deliver the phishing pages, although the organization believes the actual number is much higher.
“Most identified targets were activists, journalists, and labour union members. While some of targets had published critical opinions about Qatar’s international affairs, the majority of identified targets were affiliated with organisations supporting migrant workers in Qatar,” said activist and security researcher Claudio Guarnieri. “Interestingly, a significant number of them are from Nepal, which is one of the largest nationalities amongst migrant workers in Qatar, and a country that has featured prominently in the migrant worker narrative on Qatar.”
While experts could not find too much evidence, they believe the attacks were likely carried out by a state-sponsored actor. One of the IP addresses used to access some of the compromised email accounts had been associated with an ISP headquartered in Doha, Qatar.
However, when contacted by Amnesty, the government of Qatar denied any involvement and expressed interest in stopping the attacks. Experts pointed out that the operation could be the work of an actor that seeks to damage Qatar’s reputation.
This is not the only social engineering campaign targeting human and labor rights organizations focusing on the situation in Qatar. In December, Amnesty International published a report detailing a fake human rights organization named Voiceless Victims. It is unclear if the two campaigns are directly connected.
Related: Iranian Hackers Use Mac Malware to Steal Data
Related: Google Warns Users of Recent State-sponsored Attacks














