Apple can’t tap into iMessage conversations, thanks to end-to-end encryption, but the iPhone maker does know who you message or attempt to message with.
Earlier this year, Apple entered a spat with the FBI when it refused to unlock an iPhone that belonged to Islamic terrorist Syed Rizwan Farook, who together with his wife Tashfeen Malik, killed 14 people in a mass shooting in San Bernardino, California in December 2015. Apple at the time claimed that it couldn’t unlock the device and said the FBI was essentially asking it to create a backdoor into the iPhone.
In the end, the FBI was able to unlock the device without Apple’s involvement (it was helped by an outside party which reportedly cost more than $1 million, but the spat sparked debate over the use of backdoors. Privacy advocates, security experts, and tech companies supported Apple’s decision, arguing that available encryption products would be undermined if a backdoor was included in them.
As it turns out, Apple’s stance might have been influenced by marketing reasons too, and not purely by its determination to protect user privacy. When the Apple/FBI battle ended, the tech company emerged as a determined privacy advocate, but the incident didn’t tell the entire story. The document (below) obtained by The Intercept shows that Apple can tap into some information regarding user’s iMessage conversations, and that it does share these details with law enforcement when required to do.
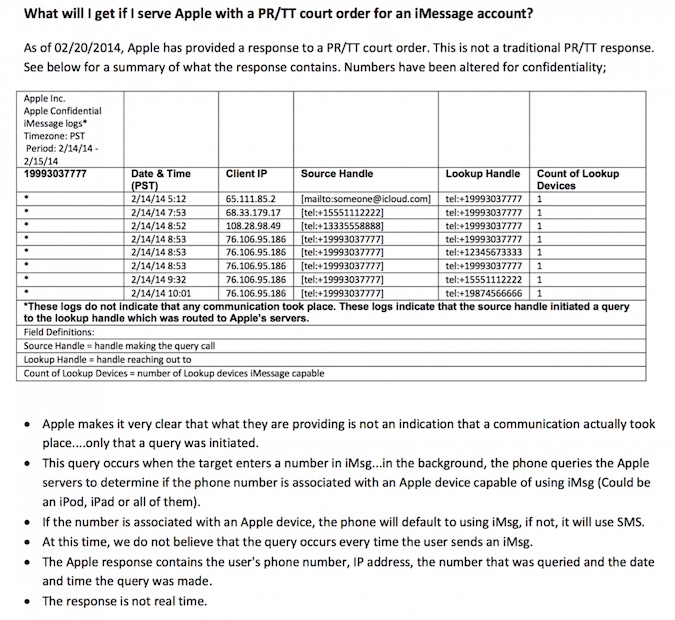
Specifically, while it can’t view the conversations you carry out with your iMessage contacts, Apple does log the queries the messaging app makes to its servers to determine whether the person you are trying to contact is using the iMessage system or not. Based on these details, a message is sent to the Messages or SMS app, and it appears in conversations either as a blue or a green bubble.
Apple’s logs record each such query and include information like your phone number, the phone number you entered, the date and time when you entered the number, and your IP address. Basically, this means that Apple knows who you were trying to contact (or at least their phone number), when you were trying to contact that person, and your approximate location at that time based on your IP address (which could be spoofed via VPN).
Not only does Apple log these details, but it also shares them with the police when court orders compel it to. While Apple says that it retains those logs for only 30 days, court orders that request such information can typically be extended in additional 30-day periods, The Intercept notes. These can be combined to create extensive lists of numbers someone has been entering.
The document, reportedly titled “iMessage FAQ for Law Enforcement,” clearly states that these logs do not offer proof that you actually contacted a number you entered in the Message app. “The document implies that Messages transmits these numbers to Apple when you open a new chat window and select a contact or number with whom to communicate, but it’s unclear exactly when these queries are triggered, and how often,” The Intercept explains.
The content of sent messages remains safe from intruding eyes, because iMessage is encrypted end-to-end, but Apple admits to be sharing requested information with the police, if that information is in its possession. “In some cases, we are able to provide data from server logs that are generated from customers accessing certain apps on their devices,” Apple told The Intercept.
“We work closely with law enforcement to help them understand what we can provide and make clear these query logs don’t contain the contents of conversations or prove that any communication actually took place,” an Apple spokesperson also said.
In the end, Apple remains true to its claim that your conversations are private and that only you and your contacts can access them, though the company does know who you might have been talking to. Apple might not be willing to weaken the security of its products by including a backdoor, but it should be more straightforward when it comes to the kind of information it can access and subsequently share with law enforcement.
Related: Video Conferencing Solution Protects Content and Metadata
Related: Researcher Proves FBI Wrong With iPhone Passcode Hack














