Expert Shows FBI Could Have Easily Hacked San Bernardino Shooter’s iPhone
A researcher has demonstrated that a known hardware hacking method could have been used to bypass the passcode retry limitations on the San Bernardino shooter’s iPhone, despite the FBI’s claims that the technique would not work.
In December 2015, Syed Rizwan Farook and his wife Tashfeen Malik killed 14 people in a mass shooting in San Bernardino, California, and they later died in a shootout with police. Investigators believed Farook’s work-issued iPhone 5c could contain important evidence, but they could not access it because the device was protected by a passcode and the security mechanisms implemented by Apple prevented brute-force attacks.
The FBI tried to convince a judge to force Apple to create a backdoor to the iPhone, but the tech giant refused, arguing that it would create a dangerous precedent. In the end, the agency managed to hack Farook’s iPhone with the help of an unidentified “outside party,” and reportedly paid as much as $1 million to get the job done.
While the FBI was trying to figure out how to access the data on the phone without triggering its security mechanisms, which could result in the data getting erased, iPhone forensics experts suggested a hardware hacking technique known as NAND mirroring. However, FBI Director James Comey said during a press conference in March that the technique would not work on Farook’s phone.
Sergei Skorobogatov of the University of Cambridge in the United Kingdom has proved the FBI wrong and demonstrated that NAND mirroring does work in these types of scenarios.
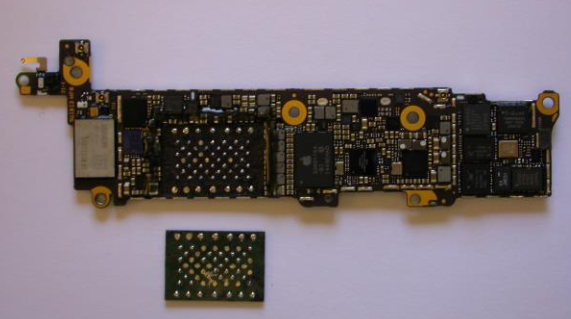
NAND mirroring involves removing the NAND flash memory chip from the device by desoldering it and creating backup copies or clones of the chip. By cloning the chip, the original memory is fully preserved while the copies can be used as many times as necessary to figure out the 4-digit passcode.
Skorobogatov conducted a successful attack using off-the-shelf components bought from an electronics distributor for less than $100.
An iPhone is disabled for one minute after six incorrect passcode entry attempts to prevent brute-force attacks. In scenarios where a backup of the NAND memory is created and the NAND is restored from this backup after every six attempts, the expert calculated that it would take roughly 40 hours to scan all possible 4-digit codes.
If the NAND chip is cloned and a number of clones are created in advance and restored in parallel while the test is being conducted, the maximum attack time decreases to 20 hours.
Skorobogatov noted that while he conducted his experiments on an iPhone 5c, iPhone 5s and 6 use the same type of NAND flash memory so it’s likely that the attack works on these models as well, although more sophisticated equipment might be needed.
It’s unclear what method has been used to crack Farook’s phone, but experts pointed out that Skorobogatov’s research once again shows that encryption backdoors are not the answer, as proposed by some U.S. lawmakers. Susan Landau, a faculty member in the Worcester Polytechnic Institute Department of Social Science and Policy Studies, noted that a better solution is to increase the security of devices while law enforcement improves its cyber security expertise.
“The moral of the story? It’s not, as the FBI has been requesting, a bill to make it easier to access encrypted communications, as in the proposed revised Burr-Feinstein bill,” Landau explained. “Such ‘solutions’ would make us less secure, not more so. Instead we need to increase law enforcement’s capabilities to handle encrypted communications and devices. This will also take more funding as well as redirection of efforts.”
Related: Multiple Passcode Bypass Vulnerabilities Discovered in iOS 9












