There are nearly 900 vulnerabilities in the Known Exploited Vulnerabilities (KEV) catalog maintained by the US Cybersecurity and Infrastructure Security Agency (CISA), including 557 CVEs that were added in 2022, according to vulnerability intelligence company VulnCheck.
VulnCheck has conducted an analysis of CISA’s KEV list and last week published a report that provides important context for the data.
There were 311 vulnerabilities in the catalog at the beginning of 2022 and it reached 868 by the end of the year. On average, more than ten exploited flaws were added to the KEV list every week in 2022.
Of the CVEs added to the list last year, 93 had a 2022 CVE identifier, which represents roughly two new actively exploited vulnerabilities per week.
VulnCheck’s analysis showed that 22 of the bugs added to the KEV last year were named vulnerabilities, including EternalBlue, Shellshock, Heartbleed, EskimoRoll, Dogwalk, SpoolFool, Dirty Pipe, ProxyNotShell, and Ripple20.
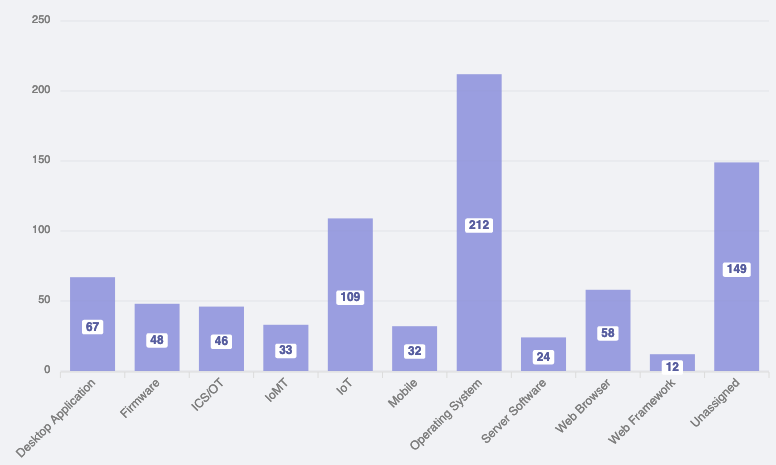
The vulnerabilities added by CISA to its catalog in 2022 impacted a wide range of products, but operating systems and IoT accounted for the highest percentages.
More than one-third of the security holes added to the ‘must-patch’ list in 2022 can be exploited for initial access.
CISA’s KEV catalog does not provide any information on the types of attacks exploiting the vulnerabilities. However, VulnCheck’s report provides such information based on the company’s own data.
The company said 241 of the 2022 additions have been exploited by threat actors (APTs), 122 by ransomware groups, and 69 by botnets.
VulnCheck has also analyzed how long it takes for a vulnerability to be added to CISA’s KEV catalog, noting that it would be a mistake for organizations to treat it as an early warning system.
In the case of the 2022 CVEs — for the older vulnerabilities this ‘time to KEV’ measurement is pointless — ten of the flaws were added on the same day or even before a public exploit or exploitation details came to light, and 38 were added within a week.
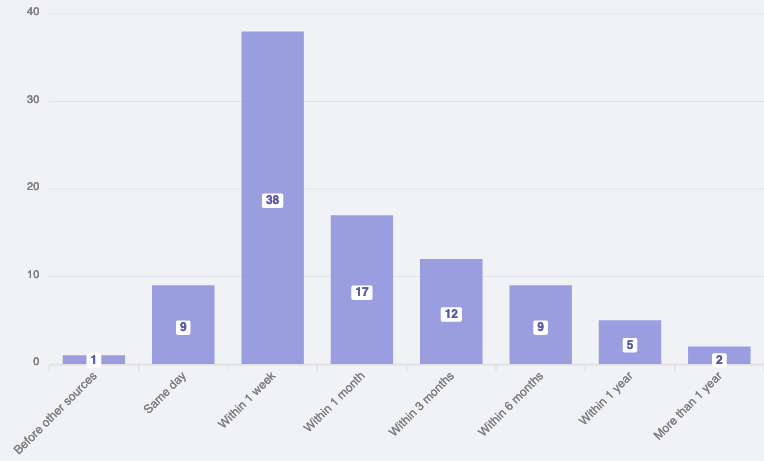
“The KEV Catalog isn’t an early warning system, but warning everyone about exploitation in the wild within a week of the first public exploit or exploitation details at a 52% rate is very respectable. Of course, that doesn’t tell the full story. There are a whole bunch of vulnerabilities published in 2022 that are known to have been exploited and aren’t on the CISA KEV list,” VulnCheck said.
Related: Exploited Control Web Panel Flaw Added to CISA ‘Must-Patch’ List
Related: Siemens Drives Rise in ICS Vulnerabilities Discovered in 2022

