More than 5,000 GitLab servers remain unpatched against a critical vulnerability allowing attackers to hijack the password reset process.
Tracked as CVE-2023-7028 (CVSS score of 10), the issue allows attackers to have password reset messages sent to unverified email addresses under their control, potentially leading to account takeover.
The flaw was introduced in GitLab 16.1.0, when a new option was added to allow users to have password reset messages sent to a secondary email address and allowed for these messages to be sent to unverified addresses.
Two weeks ago, GitLab released patches for the bug, warning that all accounts that allow logins with usernames and passwords and are not protected with second-factor authentication are affected.
Patches for the bug were included in GitLab Community Edition (CE) and Enterprise Edition (EE) versions 16.5.6, 16.6.4, and 16.7.2, and were also backported to versions 16.1.6, 16.2.9, 16.3.7, and 16.4.5.
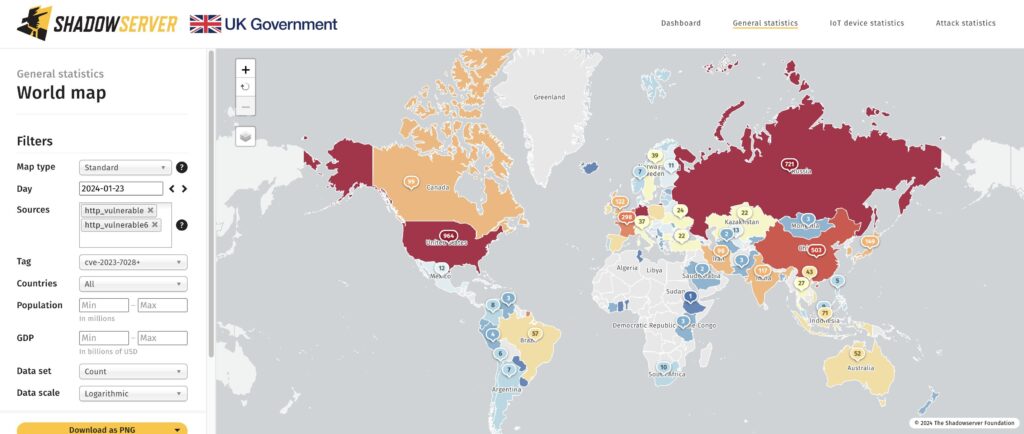
Although GitLab warned of the bug’s critical severity and urged users to update their instances as soon as possible, more than 5,000 servers remain unpatched against CVE-2023-7028, non-profit cybersecurity organization The Shadowserver Foundation warned on Wednesday.
“Running GitLab? We are sharing instances vulnerable to CVE-2023-7028 (Account Takeover via Password Reset without user interactions) – 5379 instances found worldwide (on 2024-01-23). Top: US (964) & Germany (730),” the organization said on X.
The data from Shadowserver shows that hundreds of other vulnerable GitLab servers are in Russia, China, France, and the UK as well.
Earlier this month, GitLab said that it had not observed the flaw being abused on platforms managed by GitLab, cautioning self-managed customers to review their logs for signs of exploitation and rotate all credentials if intrusions are detected.
“We strongly recommend that all installations running a version affected by the issues described are upgraded to the latest version as soon as possible,” GitLab’s advisory reads.
Related: GitLab Patches Critical Pipeline Execution Vulnerability
Related: GitLab Security Update Patches Critical Vulnerability
Related: GitLab Patches Critical Remote Code Execution Vulnerability

