Millions of Internet-of-Things (IoT) devices use the same cryptographic secrets, an oversight that exposes them to various types of malicious attacks, shows a new study by IT security consultancy SEC Consult.
Hardcoded Cryptographic Keys
Researchers have analyzed the firmware images of more than 4,000 embedded devices from over 70 vendors, including modems, routers, gateways, VoIP phones and IP cameras. A total of 580 unique private keys have been identified, the most common being SSH host keys and X.509 certificates used for HTTPS. These keys are generally used for SSH and HTTPS access to the device.
Using the Scans.io and Censys.io Internet-wide scanning services, SEC Consult has determined that at least 230 of the 580 keys are actively used. More precisely, roughly 150 of the identified server certificates are used by 3.2 million HTTPS hosts, which represents 9 percent of all HTTPS hosts on the web, while approximately 90 of the SSH keys are used by 0.9 million SSH hosts, representing 6 percent of hosts available on the Web.
According to researchers, the cryptographic keys are hardcoded into the firmware of IoT gadgets, which means all devices using certain firmware have the same keys. While in some cases the same keys are only shared across devices in a certain product line, experts also found the same keys in products from different vendors.
One example provided by researchers is a certificate found in a Broadcom software development kit (SDK). The SDK is used by companies such as Actiontec, Aztech, Innatech, Comtrend, Smart RG, Zhone and ZyXEL to develop firmware, which has resulted in the certificate being included in nearly half a million devices. A Texas Instruments SDK used by several major vendors has led to a single certificate being shared across 300,000 devices.
A malicious actor with access to the victim’s network can leverage these keys to launch impersonation, man-in-the-middle (MitM), and passive decryption attacks in an effort to obtain sensitive information. Attacks over the Internet are also possible by adversaries capable of monitoring Web traffic, SEC Consult said.
Millions of Devices Exposed on the Internet
SEC Consult’s analysis also revealed that millions of IoT devices are directly accessible via the Internet, in many cases due to insecure default configurations. A perfect example is Ubiquiti Networks, whose devices are exposed due to a default remote administration feature that the company does not want to disable. Ubiquiti products are known to be abused by malicious actors for DDoS attacks and malware distribution.
Researchers also found roughly 80,000 Seagate GoFlex network-attached storage (NAS) devices accessible on the Internet, in many cases due to a feature that enables port forwarding via UPnP.
ISPs also expose users to remote attacks by shipping modems, routers and gateways with HTTPS and SSH remote administration features enabled by default. The list of impacted ISPs includes US-based CenturyLink (500,000 exposed devices), Mexico-based TELMEX (1 million devices), Spain-based Telefonica (170,000 devices), China Telecom (100,000 devices), Chile-based VTR Globalcom (55,000 devices), Taiwan’s Chunghwa Telecom (45,000) and Australian ISP Telstra (26,000 devices).
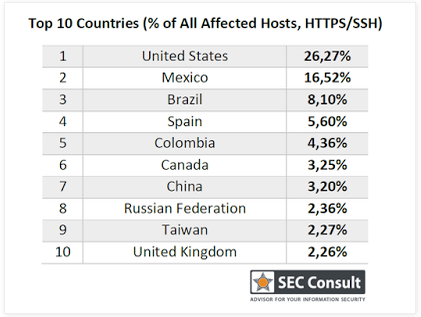
A quarter of the affected hosts have been found in the United States, followed by Mexico, Brazil and Spain.
Affected Companies and Products
SEC Consult reported identifying over 900 vulnerable products from roughly 50 vendors, but the actual number could be much higher considering that the security firm’s study only targeted firmware it had access to.
The list of affected vendors includes ADB, AMX, Actiontec, Adtran, Alcatel-Lucent, Alpha Networks, Aruba Networks, Aztech, Bewan, Busch-Jaeger, CTC Union, Cisco, Clear, Comtrend, D-Link, Deutsche Telekom, DrayTek, Edimax, General Electric (GE), Green Packet, Huawei, Infomark, Innatech, Linksys, Motorola, Moxa, NETGEAR, NetComm Wireless, ONT, Observa Telecom, Opengear, Pace, Philips, Pirelli , Robustel, Sagemcom, Seagate, Seowon Intech, Sierra Wireless, Smart RG, TP-LINK, TRENDnet, Technicolor, Tenda, Totolink, unify, UPVEL, Ubee Interactive, Ubiquiti Networks, Vodafone, Western Digital, ZTE, Zhone and ZyXEL.
SEC Consult says it has been working with CERT/CC since August to notify the affected vendors. CERT/CC has also published an advisory describing the hardcoded key issues uncovered by SEC Consult.
CVE identifiers have been assigned for some of the vendors, including Cisco (CVE-2015-6358), ZTE (CVE-2015-7255), ZyXEL (CVE-2015-7256), Technicolor (CVE-2015-7276) and Unify (CVE-2015-8251). These vendors will publish advisories to warn their customers.
Related Research
Last week at the DefCamp security conference in Romania, a team of researchers presented a study on vulnerabilities found in the firmware images of embedded devices. The study focused on security holes found in web server interfaces.
The experts performed static and dynamic analysis on a total of 1,925 firmware images from more than 50 vendors, and identified over 9,000 vulnerabilities in 185 of them. The list of issues includes cross-site scripting (XSS), file manipulation, command injection, file inclusion, information disclosure, SQL injection, and code execution flaws.
Related Reading: IoT Security Foundation Launches
Related Reading: IoT – The Security Risk Iceberg














