Researchers have uncovered a new Web-based exploit that targets Windows, Linux, and Mac OS X computers.
Users visiting a specially crafted website are prompted to run a Java applet that hasn’t been signed by a trusted certificate authority, Karmina Aquino, a senior analyst at F-Secure, wrote in a blog post July 10. If allowed to run, the applet checks the user’s operating system and delivers a payload customized for that platform, whether it’s Windows, Mac OS X, or Linux.
 Once downloaded, the malware remotely connects to an IP address to download additional components from that server. The malware on Mac OS X used port 8080, the one on Linux used 8081, and the Windows used port 8082, F-Secure researchers found. However, the researchers haven’t observed the code command-and-control server deliver additional code to infected machines, Aquino said.
Once downloaded, the malware remotely connects to an IP address to download additional components from that server. The malware on Mac OS X used port 8080, the one on Linux used 8081, and the Windows used port 8082, F-Secure researchers found. However, the researchers haven’t observed the code command-and-control server deliver additional code to infected machines, Aquino said.
“We recently came across a compromised Colombian Transport website where the malware author utilizes social engineering by displaying a signed applet upon visiting the page,” Aquino wrote.
Kaspersky Lab researchers found another website belonging to Aquaparc from Barcelona that has been injected with the same exploit, Costin Raiu, director of global research and analysis at Kaspersky Lab, told SecurityWeek. The malware downloads and runs backdoors for Linux and Windows, or a simple shell on Mac OS X. The backdoors appear to contact very complex code which communicates over an encrypted channel with other servers, Raiu said.
“The Win32 backdoor is large, about 600K; the Linux backdoor is over 1MB in size,” Raiu explained.
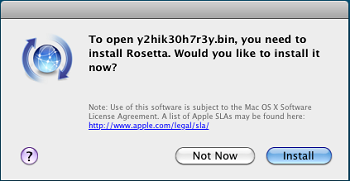 It appears the threat to Mac users is limited, as the payload is a PowerPC binary. PowerPCs were phased out about five years ago in favor of the modern Intel-based Macs, and modern Macs are vulnerable only if it has the Rosetta software installed. Rosetta, XXX, was included with OS X Leopard, made optional with OS X Snow Leopard, and dropped in OS X Lion. Unless they manually installed Rosetta, many Mac users would be safe from this specific threat for the time being.
It appears the threat to Mac users is limited, as the payload is a PowerPC binary. PowerPCs were phased out about five years ago in favor of the modern Intel-based Macs, and modern Macs are vulnerable only if it has the Rosetta software installed. Rosetta, XXX, was included with OS X Leopard, made optional with OS X Snow Leopard, and dropped in OS X Lion. Unless they manually installed Rosetta, many Mac users would be safe from this specific threat for the time being.
The Mac components were created with readily available penetration testing tools, namely TrustedSec Social Engineering Toolkit and Metasploit, said Intego Security’s Lysa Myers. The Mac malware piece “is not something that was cleverly handcrafted” and was likely created by someone who was “not especially technically savvy,” Myers said.
While rare, there have been cross-platform malware attacks in the past. The Boonana Trojan in 2010 was a Java-based exploit that affected both Macs running OS X and Windows PCs. Multi-platform attacks are a sign that Linux and Mac OS X are becoming “interesting targets” for cyber-criminals, Raiu said.
In some ways, infecting Mac OS X users may be “an easier task than for Windows, because of the mentality that you don’t get viruses on Mac,” Raiu said, noting there have been targeted attacks exploiting Microsoft Office for Mac OS X recently.
Java is especially attractive for malware developers interested in multi-platform attacks because it runs on all major operating systems without needing any tweaks. Attackers can develop malware that exploit vulnerabilities in Java, as happened earlier this year with the Flashback Trojan, which infected both Macs and Windows, but also use Java to push malware, as was the case here.
The attack was initially detected on a compromised website in Colombia, and the site as well as the command-and-control server has been reported, according to F-Secure.
Related Insight: BlackHole Exploit – A Savvy Cyber Gang Driving a Massive Wave of Fraud
















