“Disttrack” Malware Used Shamoon Attacks, Renders Hard Disks On Infected Systems Unusable
Malware being used in a new series of targeted attacks has bucked the trend, choosing to destroy the computers it infects rather than just stealing sensitive information, security researchers said.
Called “Disttrack”, the malware corrupts files, overwrites the infected machine’s master boot record, and destroys the data so that it can’t be recovered, according to reports from Symantec Security Response, Kaspersky Lab’s Global Research and Analysis Team, and McAfee on Thursday. Disttrack has been observed in the Shamoon attacks, which has already affected at least one organization in the energy sector, Symantec said, but the company declined to provide any other details about the affected organization(s).
“Threats with such destructive payloads are unusual and are not typical of targeted attacks,” Symantec said.
Disttrack appears to be made up of several components, including the initial dropper file, and two modules called wiper, and reporter. The initial infection occurs with the dropper component, or str.exe, which downloads additional files on the system, including the reporter and wiper modules, a 64-bit version of a file called trksrv.exe, and a device driver.
“The initial infection vector is as of yet unknown, but the malware has the capability of spreading via Admin$ shares” on the network, McAfee said in its report.
Once on the computer, the dropper file also installs trksvr.exe as a Windows service which starts automatically whenever the operating system starts. It creates at least four registry keys on the system.
The reporter component is named netinit.exe, but the wiper module picks its filename from a list of 29 words. The list includes words such as ctrl, dfrag, dnslookup, and power. It appears the names were chosen so that at first glance, they would look like legitimate system files.
The wiper module, whatever it is named, scans various directories, including Documents and Settings, Users, and Windows drivers, to compile two lists containing the pathnames of all the files in those folders. Affected files include documents, contents of the download, picture, video, music folders, Windows drivers, and User profiles.
All the files on the list are overwritten with an image file (looks like a grey box next to another box) so that the files are “rendered useless,” Symantec said. The two files listing the pathnames of the destroyed files are also overwritten.
“The original contents of these files are lost and not recoverable,” McAfee said in its report.
The reporter module, netinit.exe, runs the moment the trksvr service is started, and repeats every five minutes, according to McAfee. This module’s sole purpose is to report the information being collected from various directories to the malware’s command-and-control server. In a HTTP Get request, the module sends data such as the number of files that were overwritten, the IP address of the compromised machines, and a random number which acts as a unique identifier.
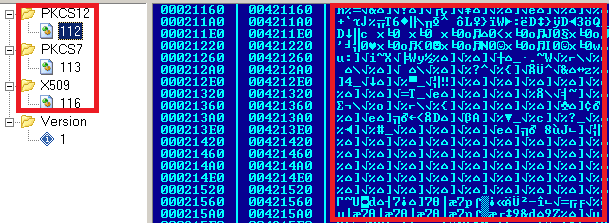
The downloaded device driver, drdisk.sys, is a legitimate device driver from a commercial applications and is used to allow programs low-level read and write access to hard disk drives. The wiper module uses the driver to overwrite the Master Boot Record (MBR) and the partition tables of the hard disk with the previously used image file.
“This renders the hard disk unusable and will not be recognized by the system after rebooting,” McAfee noted.
The driver was digitally signed with the private cryptographic key belonging to EldoS Corporation, Kaspersky Lab said.
In an analysis of the decrypted portions of the malware, Kaspersky researchers came across a string, “C:ShamoonArabianGulfwiperreleasewiper.pdb,” which seemed to hint at the earlier data-deleting malware also called Wiper, according to the Securelist post. That particular Wiper infected computers across the Middle East, particularly Iran, and deleted sensitive information from computers, earlier this year. The search for Wiper originally led to the discovery of Flame earlier this year.
“Based upon our analysis, #shamoon is NOT the malware known as ‘Wiper’, which attacked Iran in April,” Costin Raiu, director of global research and analysis at Kaspersky Lab said on Twitter.
Early this morning, SecurityWeek reported computers at Saudi Arabia-based oil company Saudi Aramco, was hit by malware. It’s not known at this time whether the malware was related to Disttrack as part of the Shamoon attacks.
“We’re aware of the malware and will continue to monitor the situation. There are allegations that it has infected at least one energy company, possibly two, but it’s not clear if they were specific targets or infected by random chance,” researchers from the Tactical Analysis Center (TAC) of EnergySec, a non-profit that supports organizations within the energy sector in securing their critical technology infrastructures told SecurityWeek via email. “The destructive nature of this malware isn’t consistent with other targeted instances and, as of now, we have no indication that the situation warrants heightened measures. This may be a case of malware being highlighted given the [appropriate, in our opinion] attention on critical infrastructure security.”
















