The website of American gunmaker Smith & Wesson was hacked late last month and the hackers planted malicious code designed to steal customers’ payment card information
According to Willem de Groot of Netherlands-based ecommerce fraud protection company Sanguine Security, the attackers planted a payment skimmer on the Smith & Wesson online store on November 27.
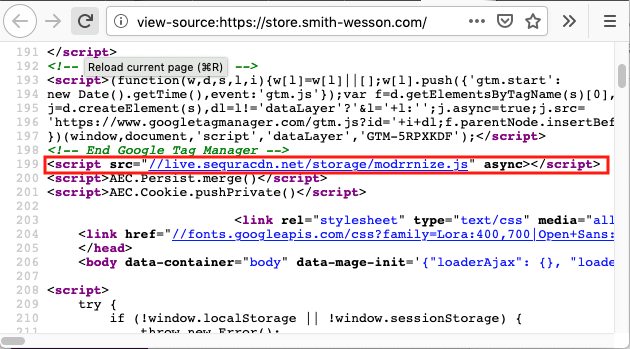
The expert has pointed out that the Smith & Wesson store loads malicious code from a domain set up by the attackers. The skimmer captures personal and financial information entered by users on the checkout page and sends it to the cybercrooks.
The attack appears to be the work of one of the several threat groups specializing in Magecart attacks, which involve planting credit card skimmers either directly on the targeted online stores or through companies providing services to online shops.
De Groot says the skimming code and infrastructure used in the Smith & Wesson attack is identical to one spotted in a campaign impersonating Sanguine Security. In that operation, Magecart hackers registered fake Sanguine Security domains under De Groot’s name, and they used those domains to “funnel stolen payments.”
Magento contributor Daniel Ruf suggested that the attackers exploited a known vulnerability in the Magento ecommerce platform to hack the Smith & Wesson website. SecurityWeek can confirm that the Smith & Wesson online store appears to run on Magento.
Magento issued a warning recently, urging customers to install patches for a remote code execution vulnerability that can be exploited by unauthenticated hackers to deliver malware.
SecurityWeek has reached out to Smith & Wesson for comment and will update this article if the company responds. The malicious code is still present on the organization’s website at the time of writing.
The official website of Macy’s was also compromised recently as a result of a Magecart attack and the company’s stock dropped 10 percent after news of the data breach broke.
Related: Magecart Attack on eCommerce Platform Hits Thousands of Online Shops
Related: Magecart Hackers Target Mobile Users of Hotel Websites















