A wealthy Russian businessman with ties to the Kremlin was sentenced Thursday to nine years in prison for his role in a nearly $100 million stock market cheating scheme that relied on secret earnings information stolen through the hacking of U.S. computer networks.
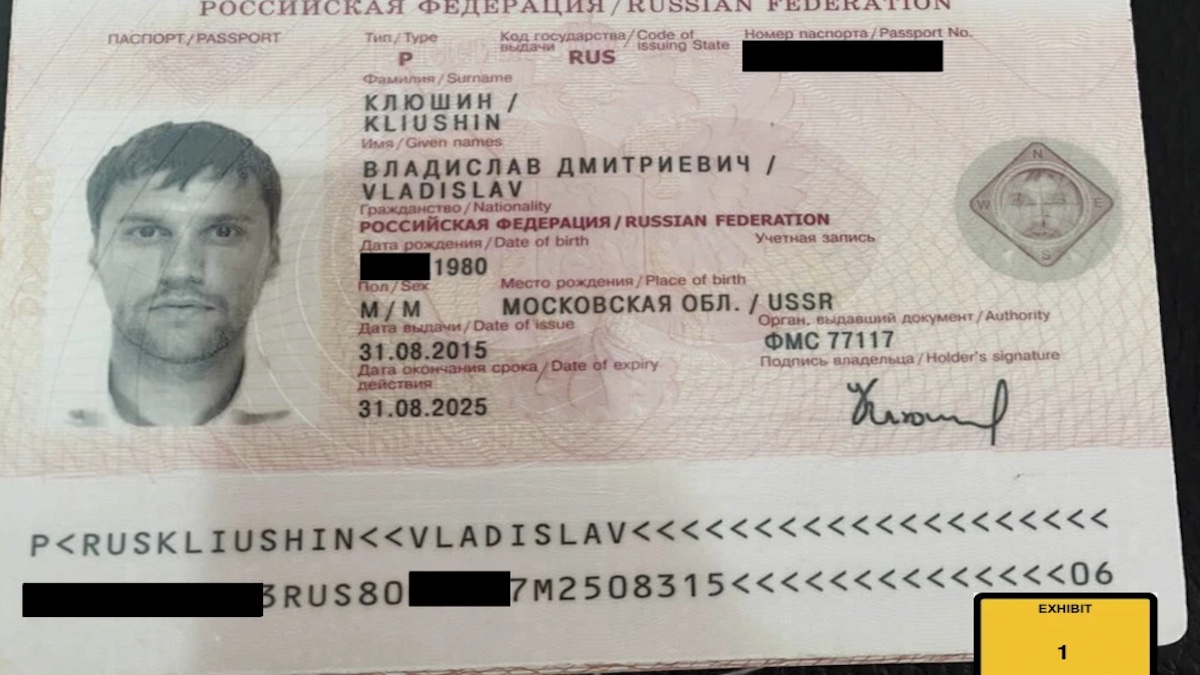
Vladislav Klyushin, who ran a Moscow-based information technology company that did work for the highest levels of the Russian government, was convicted in February of charges including wire fraud and securities fraud after a two-week trial in federal court in Boston.
Authorities say he personally pocketed more than $33 million in the scheme, which involved breaking into computer systems to steal earnings-related filings for hundreds of companies — including Microsoft and Tesla — and then using that insider information to make lucrative trades.
Klyushin, 42, has been jailed in the U.S. since his extradition in 2021, and the more than two years he’s been detained will be credited to his prison term. He was arrested in Switzerland after arriving on a private jet and just before he and his party were about to board a helicopter to whisk them to a nearby ski resort. After he completes his sentence, he’s expected to be deported to Russia.
Klyushin, who walked into the courtroom in handcuffs, sat at a table with his attorneys and listened to an interpreter through headphones as lawyers argued over the sentence. At the advice of his attorney, he declined to address the judge before she sentenced him.
Four alleged co-conspirators — including a Russian military intelligence officer who’s also been charged with meddling in the 2016 presidential election — remain at large, and even though prosecutors allege in a court filing that they’re still “likely sitting at their keyboards,” they acknowledge that they four will likely never be extradited to the U.S. to face charges.
Prosecutors had sought 14 years in prison, saying a stiff punishment was crucial to send a message to overseas cybercriminals. Assistant U.S. Attorney Seth Kosto told the judge that Klyushin has accepted no responsibility for his crimes and that once he serves his sentence, he’ll return to Russia, where he is a “powerful person” with “powerful friends in the highest echelons of Russian society.”
“Hackers will be watching this sentence to decide whether it’s wroth engaging in this kind of conduct,” Kosto said.
Prosecutors say the hackers stole employees’ usernames and passwords for two U.S.-based vendors that publicly traded companies use to make filings through the Securities and Exchange Commission. They then broke into the vendors’ computer systems to get filings before they became public, prosecutors said.
Armed with insider information, they were able to cheat the stock market, buying shares of a company that was about to release positive financial results, and selling shares of a company that was about to post poor financial results, according to prosecutors. Many of the earnings reports were downloaded via a computer server in Boston, prosecutors said.
Klyushin has denied involvement in the scheme. His attorney told jurors that he was financially successful long before he began trading stocks and that he continued trading in many of the same companies even after access to the alleged insider information was shut off because the hacks were discovered.
Defense attorney Maksim Nemtsev called prosecutors’ prison request “draconian,” adding that there is “no reason to think that he would would risk the well-being of his family again by committing crimes.”
His lawyers asked the court for leniency, saying Klyushin had no prior criminal history and has already been seriously punished. He spent months in solitary confinement in Switzerland while awaiting extradition to the U.S. and his company has lost multimillion dollar contracts, his attorneys wrote.
Klyushin owned a Moscow-based information technology company that purported to provide services to detect vulnerabilities in computer systems. It counted among its clients the administration of Russian President Vladimir Putin and the Ministry of Defense, according to prosecutors.
Klyushin’s close friend and an alleged co-conspirator in the case is military officer Ivan Ermakov, who was among 12 Russians charged in 2018 with hacking into key Democratic Party email accounts, including those belonging to Hilary Clinton’s presidential campaign chairman, John Podesta, the Democratic National Committee and the Democratic Congressional Campaign Committee. Ermakov, who worked for Klyushin’s company, remains at large.
Prosecutors have not alleged that Klyushin was involved in the election interference.