Europol on Tuesday announced the shutdown of VPNLab, a VPN service that had often been used by cybercriminals.
VPNLab has been shut down after law enforcement authorities seized 15 servers across 10 countries. Police in Germany, the Czech Republic, France, Latvia, Hungary, Ukraine, the UK, the US, and Canada took part in the operation.
Europol said VPNLab was launched in 2008, promising online anonymity for as little as $60 per year. Advertised on the dark web, the VPN service was used by many cybercriminals, including in the distribution of ransomware and other malware.
The law enforcement operation started after an attack on a German city in August 2019.
According to authorities in Germany, the service was used, among others, by Ryuk ransomware operators.
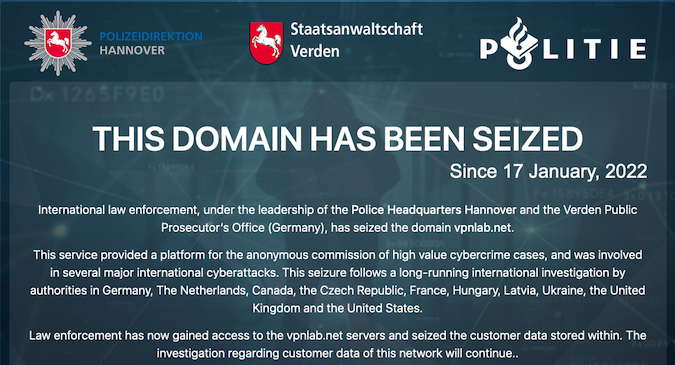
The VPNLab domain, vpnlab.net, currently displays a message informing visitors that the domain has been seized by law enforcement. The message claims authorities have obtained customer data stored on seized servers and an investigation has been launched.
“As a result of the investigation, more than one hundred businesses have been identified as at risk of cyberattacks. Law enforcement is working directly with these potential victims to mitigate their exposure,” Europol said.
VPNLab is not the only VPN service targeted by law enforcement in recent years due to its use by cybercriminals. In December 2020, Europol announced the disruption of a service called Safe-Inet.
Related: Europol Ordered to Delete Data Not Linked With Crime
Related: Europol Announces Arrests of 7 People Linked to REvil, GandCrab Ransomware
Related: Europol Report Highlights Pandemic’s Effect on Cybercrime

