The internet is already being scanned for VMware vCenter servers affected by CVE-2021-22005, a critical vulnerability for which the virtualization giant announced patches just a couple of days ago.
VMware on September 21 informed customers that updates released for its vCenter Server product patched 19 vulnerabilities, including a critical arbitrary file upload flaw affecting the Analytics service.
“A malicious actor with network access to port 443 on vCenter Server may exploit this issue to execute code on vCenter Server by uploading a specially crafted file,” VMware said in its advisory.
The company urged users not to ignore the advisory, warning them that attackers who may have breached their systems could have access to vCenter servers from inside the corporate network.
On September 22, threat intelligence company Bad Packets already reported seeing scanning activity targeting CVE-2021-22005. Bad Packets said the scans were looking for vulnerable systems by leveraging a workaround test shared by VMware.
The same test has also been added to at least one open source vulnerability scanner so it’s possible that not all scanning activity is malicious.
Bad Packets said it detected scanning activity from several hosts, but clarified that it did not appear to be mass scanning due to the fact that only some of its honeypots were targeted.
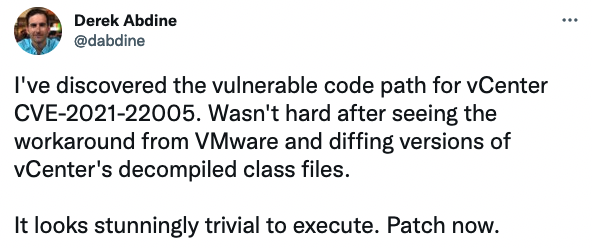
Derek Abdine, the CTO of internet scanning service Censys, claimed on Twitter that he discovered the vulnerable code path for CVE-2021-22005 and warned that it’s “stunningly trivial to execute.”
Cybersecurity firm Rapid7 identified more than 2,700 vulnerable vCenter servers exposed to the internet, but noted that this is likely only a fraction of affected systems. “[Attackers] with existing network ingress will be tempted to utilize that access to take advantage of this vulnerability,” the company warned.
VMware vCenter has been targeted by threat actors in recent months. Attacks exploiting CVE-2021-21985, a vulnerability disclosed in May, started roughly one week after VMware announced the availability of patches.
Related: Russian Hackers Exploiting Recently Patched VMware Flaw, NSA Warns
Related: Critical VMware vCenter Server Flaw Can Expose Organizations to Remote Attacks












