VMware informed customers on Monday that the recently disclosed Apache Struts2 vulnerability, which has been exploited in the wild over the past week, affects several of its products.
The remote code execution vulnerability, tracked as CVE-2017-5638, has been described by VMware as “catastrophic.” The issue impacts versions 6.x and 7.x of the VMware Horizon Desktop-as-a-Service (DaaS) platform, vCenter Server 6.0 and 6.5, vRealize Operations Manager (vROps) 6.x, and vRealize Hyperic Server 5.x.
vCenter 5.5 is not affected. Until fixes become available for vCenter 6.0 and 6.5, users can disable the performance charts service to prevent potential attacks. However, VMware noted that applying the workaround will cause Overview Performance Charts to become unavailable in vSphere Web Client.
Cisco has also launched an investigation to determine which of its products are affected. The networking giant initially identified three products, but the number has now reached 10 and there are still several devices and services under investigation.
Attacks in the wild
This Apache Struts2 vulnerability exists in the Jakarta Multipart parser and is caused by the improper handling of Content-Type header values. A remote, unauthenticated attacker can exploit the flaw to execute arbitrary commands by sending a specially crafted HTTP request.
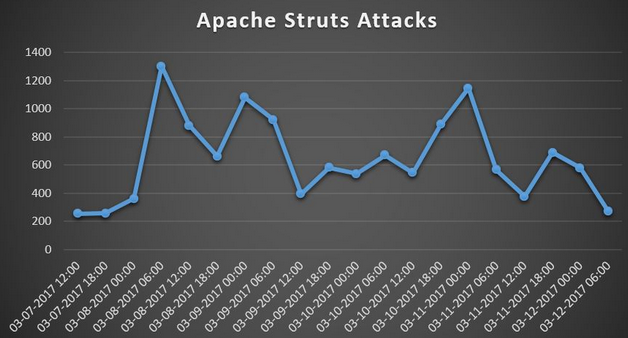
The security hole was patched on March 6 with the release of versions 2.3.32 and 2.5.10.1, and the first attacks were observed one day later, after a proof-of-concept (PoC) exploit was made public.
Imperva reported seeing thousands of attack attempts in the days following March 7. The attacks were traced to more than 1,300 IP addresses across 40 countries, including China and the United States, which accounted for 67 percent and 17 percent of the attempts, respectively.
According to data from Imperva, 90 percent of attackers focused their efforts on less than 10 applications, while the rest targeted as many as 181 apps.
A majority of the attacks observed by the security firm were attempts to determine if the targeted web application had been vulnerable, but researchers also noticed attempts to create files.
In some cases, the hackers had tried to download and execute files from a remote server. A control panel found on one of these servers showed that some of the files had been downloaded hundreds of times.
The Canada Revenue Agency (CRA) shut down its website for roughly 48 hours last week after learning of the Struts vulnerability. The organization said its site had been taken offline as a precaution, not as a result of a successful breach.
Hackers did manage to breach Statistics Canada’s website by exploiting the flaw, but officials said no sensitive data was compromised, CBC reported.













