The challenges organizations face in developing cyber skills have never been more acute. Too often, security teams find themselves locked into reactive modes, continuously responding to immediate threats without being afforded the time to learn from them, so there’s no opportunity to cross-train and upskill is missed.
In many cases, organizations simply don’t take the time, or have the background, to craft a roadmap that allows them to measure and improve cyber competencies. Developing this roadmap can be time-consuming and expensive but, fortunately, there is a better option — a framework called the Defense Readiness Index (DRI).
What is DRI?
DRI is inspired by the Cybersecurity Maturity Model Certification, a program initiated by the United States Department of Defense in order to measure defense contractors’ capabilities, readiness, and cyber security sophistication.
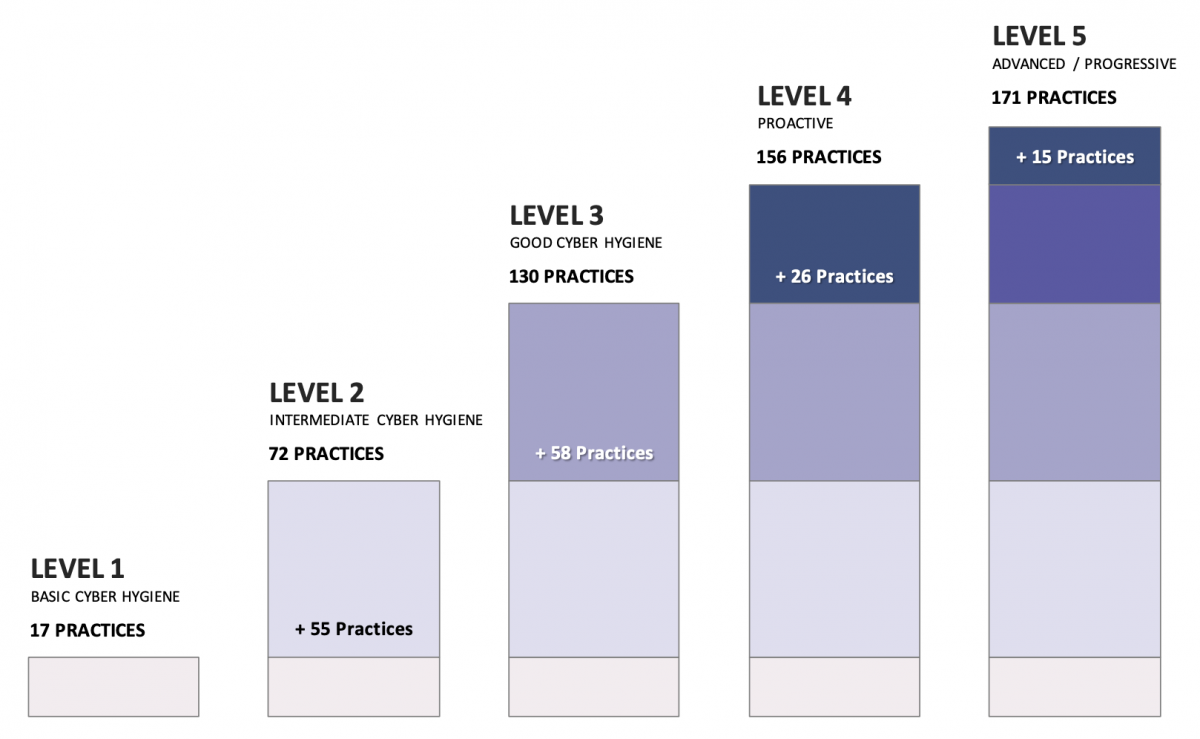
DRI has five levels of controls and practices. The first level covers basic cyber hygiene. At this level there are no defined differences in security practitioner roles (such as security management, engineering, and analysis). Higher indexes add more controls and practices, rising from Intermediate Cyber Hygiene to Good Cyber Hygiene, to Proactive, to Advanced/Progressive.
DRI delivers a robust, quantitative threat model that is meaningful to companies. Organizations typically spend large amounts of money with consultants doing threat modeling, before figuring out needed controls. DRI delivers modeling and controls that satisfy most organizations’ broad use cases.
To maximize the usefulness of DRI, organizations should define their target DRI based on the types of threats they expect to face, not just current ones.
Key Benefits of DRI
Using DRI gives an organization an accurate measurement of where its team stands in terms of its competency for defending against cyber attacks. Ideally, DRI looks at the team’s mix of demonstrated skills, capabilities to detect and disrupt threats, ability to collaborate on an investigation, and the overall makeup of the team itself.
Ideally, a team focused on the higher DRI levels would be appropriately staffed and have the tools in place required to do their job. Where possible, DRI should incorporate team-based threat exercises that enable an organization to validate the technical and soft skills of the team, and to see how well it performs in simulated detection and response situations.
DRI allows an organization to apply rankings for skills development planning. When an organization aligns these rankings with the content at each level of the DRI model, it provides a roadmap to focus on the skills needed to move up to the next level, or to remain at the same level.
DRI also lays the groundwork for an organization to achieve its optimal level of cyber readiness. By analyzing DRI rankings, it’s possible to determine which skills need to be improved or developed, what roles need to be filled, and the associated costs.
Finally, DRI enhances assessment and reporting mechanisms allowing an organization to see the progress a team is making, and to plan necessary improvements. In addition, DRI provides data to report to senior management and the board of directors about the strength of the security team.
How to implement DRI
Set priorities. Make a list of the security concerns and issues that are the most important to the organization.
Assess the security team’s capabilities. Make an honest and realistic assessment of the team’s weaknesses as well as strengths, noting key areas for improvements.
Calculate the organization’s DRI score. This is achieved using a combination of data from security team assessments, the technical tools being used, and the personal skills of individuals. The score will decay over time, because the threat landscape changes, priorities change, and new technologies replace old ones. To maintain the desired DRI score, organizations need to continually build people’s skills so they are able to defend against evolving threats.
Develop a plan for reaching the organization’s optimal DRI level. This entails drawing a detailed picture of the organization’s security team and determining how best to align security priorities with available personnel. Obvious issues are looking at how large and skilled the team is; and whether there are enough advanced analysts, threat hunters, and SOC engineers to deal with the current and forecasted level of threats.
As with all new initiatives, it’s important not to waste time and resources on issues and skills that are secondary or irrelevant. In embracing DRI, remember that the process is a journey, not a destination, as work is never done and things change constantly.
Keeping pace with the evolving cyber threat landscape requires a continuous program to advance cyber security skills within an organization. DRI is a reliable alternative for assessing a security team’s skill level, developing a roadmap for improving cyber competencies, and reaching the optimal level of cyber security readiness.

