TXOne Networks this week unveiled a new security appliance designed to help small and medium-sized manufacturers protect their operational technology (OT) networks against cyber threats.
The new appliance, named EdgeIPS Pro 216, is compact and it can be deployed in a cabinet or IT rackmount.
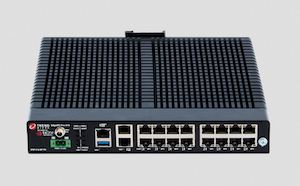 The product, advertised as ideal for harsh environments, leverages one-pass deep packet inspection technology, and offers IPS-based network segmentation with ICS/OT protocol filtering. Other capabilities include virtual patching and antivirus scanning.
The product, advertised as ideal for harsh environments, leverages one-pass deep packet inspection technology, and offers IPS-based network segmentation with ICS/OT protocol filtering. Other capabilities include virtual patching and antivirus scanning.
“By deeply analyzing network traffic on levels 2 through 7 and allowing for interoperability between key nodes, EdgeIPS Pro 216 provides attack information, event logs, early attack detection, and trust list-based filtering of control commands,” TXOne says.
The device has eight sets of paired ports, provides 2Gbps of bandwidth, and supports a wide range of industrial protocols.
EdgeIPS Pro 216 is expected to become available worldwide in July.
TXOne Networks is a joint venture between cybersecurity firm Trend Micro and industrial networking solutions provider Moxa. The new company was announced in November 2018 and unveiled its first product, an IPS, in April 2019.
Related: Trend Micro Unveils New OT Endpoint Security Solution Made by TXOne
Related: Honeywell Launches New OT Cybersecurity Solution for Commercial Buildings
Related: NIST Releases ICS Cybersecurity Guidance for Manufacturers















