Twitter has permanently banned the account of Distributed Denial of Secrets (@DDoSecrets) after it posted links to stolen information belonging to hundreds of law enforcement organizations in the United States.
Distributed Denial of Secrets (DDOS), a WikiLeaks-style organization whose goal is the “free transmission of data in the public interest,” recently leaked roughly 270 GB of information on more than 200 police departments, fusion centers, the FBI and other law enforcement organizations.
The files, collectively named “BlueLeaks,” were allegedly provided to DDOS by hackers who are part of the Anonymous hacktivist movement. The files appear to originate from Netsential, a Texas-based web development company, which reportedly admitted being breached through a compromised customer account.
Journalist and activist Emma Best, one of the main people behind DDOS, reported on Tuesday that Twitter permanently suspended the organization’s account. Twitter said it suspended the account for violating rules “against distribution of hacked material.”
“We don’t permit the use of our services to directly distribute content obtained through hacking that contains private information, may put people in physical harm or danger, or contains trade secrets,” Twitter said in the email announcing its decision to suspend the account.
Best told Wired they have tried to remove certain types of information from the leaked files, including details on crime victims, children, private businesses, healthcare firms and veterans associations, but admitted that they may have missed some things.
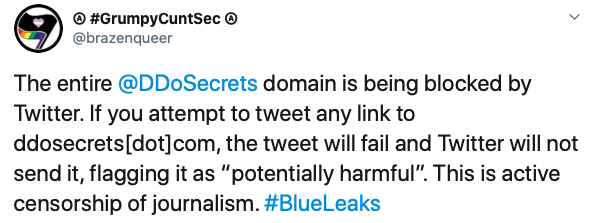
Twitter is also preventing users from posting links to the DDOS website, telling them that the link has been identified as “potentially harmful.” When users try to access previously posted links, they are informed that the link could point to a website that phishes personal information, installs malware, or violates Twitter’s terms of service.
The National Fusion Center Association (NFCA), which has confirmed the validity of the leaked files, raised concerns that threat actors could leverage the information to target law enforcement organizations and their employees.
Ilia Kolochenko, founder and CEO of web security company ImmuniWeb, who also has a master’s in criminal justice and cybercrime investigations, pointed out that the leak could have serious consequences for many innocent people.
“First, it will likely inflict irreparable reputational, financial and even physical harm to suspects and people charged with crimes who later were acquitted in a court of law,” Kolochenko said. “Furthermore, it will jeopardize legally protected people, like witnesses, who helped investigators convict dangerous criminals. The disclosure will now literally cause the death of the witnesses if their identity is revealed to the criminals or their bloodthirsty accomplices. Finally, it will substantially hinder the performance of daily law enforcement operations across the entire country, bolstering street crimes and violent crime, exposing thousands of helpless people to the risk of serious bodily injuries and death.”
Some supporters of DDOS’s work have claimed that none of the leaked files are classified, while others pointed out that WikiLeaks and other similar entities have not had their accounts suspended by Twitter despite posting links to information obtained through hacking.

Related: Police Officers’ Personal Info Leaked Online
Related: Twitter Suspends Fake Accounts for Exploiting API Vulnerability













