A new piece of ransomware analyzed by researchers from iSIGHT Partners uses visual components borrowed from CryptoLocker and CryptoWall.
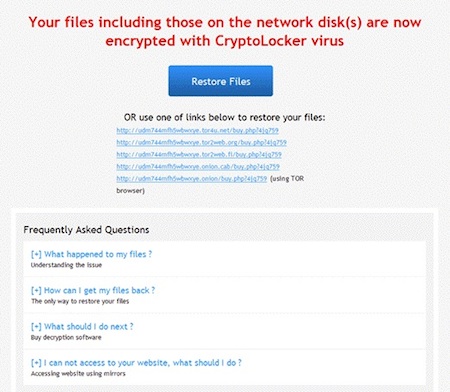
Dubbed TorrentLocker, the malware is not different from other file encryptors. Once it infects a computer, it encrypts the victim’s most valuable files using the Rijndael algorithm (symmetric cipher) and holds them for ransom. What’s interesting about this threat is that while its code is unique, the ransom message informs victims that their files have been encrypted by the “CryptoLocker virus,” and the ransom page and the FAQ section look like the one from CryptoWall, researchers said.
 For persistence, the malware and its configuration reside in the Windows Registry in HKCUSoftwareBit Torrent ApplicationConfiguration, hence the name TorrentLocker.
For persistence, the malware and its configuration reside in the Windows Registry in HKCUSoftwareBit Torrent ApplicationConfiguration, hence the name TorrentLocker.
Experts haven’t been able to determine if the malware is sold on underground forums.
The TorrentLocker samples analyzed by iSIGHT Partners are distributed via spam messages and they appear to be targeting users located in Australia. The ransom fee must be paid in Bitcoin, but the amount of money victims have to pay in order to recover their files is shown in Australian dollars. Furthermore, the recommended Bitcoin sellers are all located in Australia.
CryptoLocker was disrupted at the beginning of summer and victims have a chance to recover their files thanks to a new service launched by FireEye and Fox-IT. However, researchers believe that TorrentLocker might adopt the notoriety of CryptoLocker by spoofing its visual components.
“It may also cause victims to assume that their files are encoded in RSA-2048, a possibly more secure encryption method than the Rijndael algorithm used to encrypt files in TorrentLocker,” Richard Hummel, senior technical intelligence analyst at iSight Partners, explained in a blog post.
On the other hand, the threat might not be widely used by cybercriminals because it lacks distinguishing features. Another problem with TorrentLocker is that it communicates with its command and control (C&C) server, which is hardcoded into the malware, before encrypting files. Similar to the case of CryptoLocker, if the C&C infrastructure is disrupted, the ransomware will not be able to encrypt files.
“We’ve seen a number of different malware variants using the name ‘Cryptolocker’ due to the media attention surrounding it. The files ‘encrypted’ by some of these malware variants CAN be recovered without paying the ransom,” Tom Cross, director of security research at Lancope, told SecurityWeek. “However, because people know that files encrypted by the original ‘Cryptolocker’ malware cannot be recovered, they often pay ransoms to these copycat operators. It may not be possible to recover files encrypted by the TorrentLocker variant, but regardless, it’s important that victims figure out exactly which variant they have been infect with, as in some cases the files are recoverable.”
“Furthermore, we advise against anyone paying a ransom to a ransonware gang. Those payments help fuel this criminal activity and finance attacks against other victims. There are lots of ways to loose a hard drive. The best approach is to have good backups,” Cross added.
While TorrentLocker lacks distinguishing features, other file encryptors employ some innovative techniques. For example, the recently discovered CTB-Locker (Critroni) uses Tor to communicate with its C&C server and it relies on an unusual cryptographic scheme to ensure that files can’t be decrypted unless the ransom is paid.

