The three primary trends in the incidence of destructive cyber-attacks are that they are increasing; they are usually state-sponsored; and they do not, apart from a few rare occurrences, involve anything more than basic tools. Potentially more concerning for private industry, however, is a lack of concern over what, in kinetic warfare, would be termed ‘collateral damage’.
Cybereason, a Boston MA-based threat hunting firm, has analyzed destructive cyber-attacks from the 1982 software-instigated explosion in a Siberian pipeline to the recent NotPetya and Industroyer attacks. Cybereason’s conclusions are not reassuring for industry.
A graph of attack sophistication over time shows two primary characteristics. The majority of attacks have occurred since 2012, and the majority of attacks are (relatively) unsophisticated.
The three sophisticated attacks are a 1998 US military attack against Serbian air defense systems; the Stuxnet attack against the Iranian nuclear program in 2010; and the CrashOverride/Industroyer attack against the Ukrainian power grid in 2016. All three have one common characteristic: they are thought to be nation-state attacks against critical or military infrastructure.
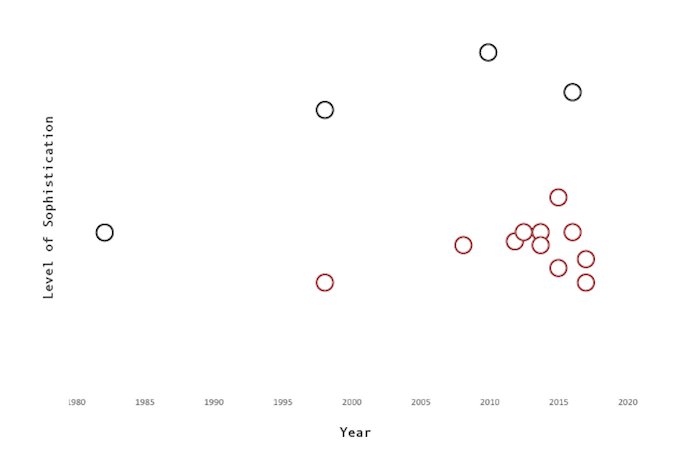
A clear majority of unsophisticated attacks are targeted against private industry. Cybereason sees little sign of this being contained by government interaction, and fears that it is likely to increase: it is, in effect, uncontrolled cyber war in all but official classification.
Some of these attacks are likely to have been nation-state actors testing out their cyber-weapons. The 2015 attack against the French television station TV5Monde is thought to be one; where the UK intelligence community concluded that it was likely an attempt to test forms of cyber-weaponry as part of an increasingly aggressive posture by Russia, acting through APT28/Fancy Bear.
Other attacks are purely political, including several attacks by Iranian hackers against Saudi oil production. Some could be considered ‘national’ political/revenge, such as the North Korean Dark Seoul attack against South Korean television and banking in 2013, and against Sony Pictures in 2014.
Cybereason argues that government is unable — perhaps unwilling — to counter this threat.
“There is no incentive for nations to stop this behavior,” Cybereason explains in its report (PDF). “They can signal displeasure, retaliate for another’s actions, or conduct disruptive covert operations with impunity. The relative ease in striking internationally that the Internet provides combined with the comparative lack of retribution has created an environment where nations will continue to experiment and grow increasingly bold in their attacks.”
The problem for private industry, however, is the fundamental difference between kinetic and cyber warfare. “The idea that a major power would threaten the critical infrastructure of another major power over an information operation would be outrageous if the threat was carried out via kinetic means.”
But governments are reluctant to respond in the cyber domain as they would in the kinetic domain for fear of escalation ultimately leading to the transition from cyber to real world conflict. The result is that cyber collateral damage is largely accepted by governments; and that collateral damage is frequently private industry.
“With no ability, or even intent to dissuade destructive attacks from nation states,” warns Cybereason, “the private sector is paying the ultimate price. They are most often the victims of these attacks because they are both less secure than government networks and also have been largely deemed a ‘safe’ target from a retaliation standpoint.”
For this reason, Cybereason believes “that the cluster of relatively low sophisticated [nation-state] attacks is likely to continue grow year over year. The victims will likely continue to be non-government institutions that for some reason or other present a useful target for advancing a hostile nation’s interests.”
It is equally worried, however, that similar tactics will be adopted by non-state attackers.
“Currently, DDoS is the easiest and most leveraged tool for hacktivists and those looking to disrupt specific entities,” the security firm says. “However, as more destructive tools continue to be used and society continues to become numb to the announcements of new attacks, cybercrime and hacktivists will increasingly be willing to move into this space. The ability to have a larger impact combined with the ability to increase obfuscation by not only damaging the information systems but also wiping forensic evidence will become even more enticing for those who want to expand their business model.”
Put simply, Cybereason believes that private sector attackers will increasingly use destruction as part of their methodology. The implication, and advice from Cybereason, is that the private sector defenders need to factor aggressive destruction into their risk management.
It warns against relying on ‘deterrence by denial’, whether this is a government induced threat of retaliation or private sector ‘hacking back‘. Government will be reluctant to instigate the former, while the latter “is only going to lead to more hacking, less secure networks, and in general a shorter and more brutal life for corporation’s network security.”
It recommends two courses of action for the private sector. The first is to understand and recognize where it might be a target for “a nation state lashing out” now, and possibly destructive hacktivist attacks in the future. This implies that effective disaster recovery can no longer be considered a luxury but an absolute necessity. The second is to switch from reactive defense to proactive threat-hunting within the network, in order to detect and block destructive attacks before they can be triggered by the adversary.
In June 2017, Cybereason announced that it had raised $100 million in Series D funding, increasing the total investment in the firm to $189 million.














