Threat actors could target DNA researchers with malware in an effort to modify synthetic DNA orders and create pathogens or toxins, researchers warn.
In a newly published article in Nature, a group of academic researchers from Israel’s Interdisciplinary Center Herzliya and Ben-Gurion University of the Negev detail a cyberattack that exploits gaps within the security of the DNA procurement process for malicious purposes.
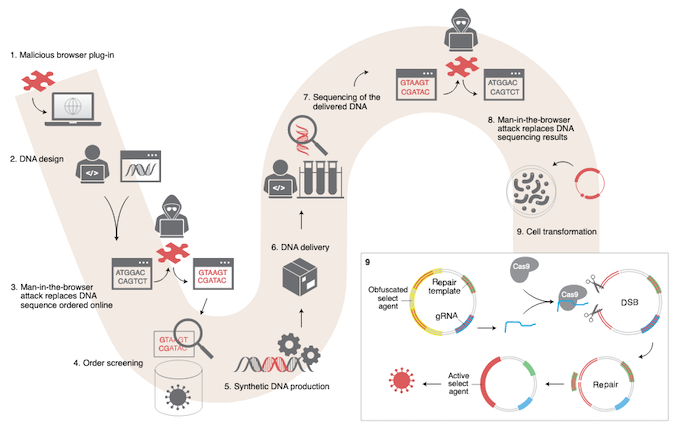
Aimed at underlining the need for convergence between cybersecurity and biosecurity, the attack presumes that an attacker is able to compromise the computer of a researcher with an academic institution and alter orders placed with a DNA synthesis company.
Because the software editors and file formats currently used when ordering synthetic DNA do not ensure the electronic integrity of orders, the attacker could replace either parts of or all of the researcher’s order with malicious sequences.
By using DNA obfuscation, similar to the obfuscation methods employed by cyber-actors for their malicious code, the attacker ensures that the pathogenic DNA is camouflaged.
While the DNA synthesis provider would check the order against a database of problematic sequences, (they are required to check every subsequence of 200 consecutive base pairs, with human inspection employed to verify suspicious sequences), obfuscation ensures that only legitimate matches are returned.
Thus, the report accompanying the delivered product shows the DNA as error-free, and the malware ensures that, even if the researcher seeks additional confirmation, the results would display the originally-requested sequence, and not the modified one.
However, as soon as the researcher inserts “the plasmid containing the obfuscated agent into Cas9-expressing cells, the DNA, deobfuscated by CRISPR-Cas9, will allow the expression of the gene encoding a noxious agent,” the Nature article reveals.
The researchers said they were able to insert an obfuscated DNA encoding a toxic peptide and that the software designed to implement the screening guidelines did not detect it.
Such attacks, the researchers note, can be mitigated through improved cybersecurity protocols, including electronic signatures, intrusion detection, behavioral analysis fueled by artificial intelligence, and the like.
“Without a comprehensive penetration testing of the screening frameworks, some pathogenic sequences will fall through the oversight cracks,” the researchers point out.
Related: Website Security Breach Exposes 1 Million DNA Profiles
Related: Critical Vulnerabilities Found in Popular DNA Sequencing Software












