Symantec on Wednesday unveiled a new product designed to protect critical infrastructure organizations, including industrial and Internet of Things (IoT) environments, against USB-borne threats.
Industrial Control System Protection (ICSP) Neural is a network-integrated USB scanning station that should make it easier for organizations to ensure that the USB drives used to transfer data between devices are not infected with malware.
ICSP Neural leverages Symantec malware and threat intelligence capabilities, along with file reputation ratings to detect and neutralize malicious files. Additionally, each suspicious file is executed in a lightweight virtual machine to identify both known and unknown threats.
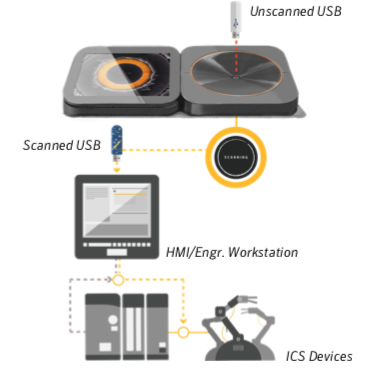
The new product also comes with an optional enforcement driver that is installed on endpoints to ensure that USB drives that have not been scanned cannot be used. The enforcement driver is an MSI package with a size of less than 5 Mb and it works on any type of operating system, even legacy systems such as Windows XP.
The driver blocks unscanned USBs and allows scanned devices to be connected. However, in an effort to avoid having to constantly re-scan devices while performing maintenance, only files added by the user after scanning are made inaccessible, Symantec told SecurityWeek.
The USB scanning station can be deployed in industrial organizations in convenient locations, explained Kunal Agarwal, general manager of Symantec’s Internet of Things division. For example, in the case of a vessel, scanners can be placed in each of the 2-3 control rooms. In manufacturing plants, each manufacturing line can have its own station.
Agarwal said organizations typically deploy the ICSP Neural device in the vicinity of operational systems. In the case of more dense facilities, such as in the healthcare sector, the scanner can be placed at the entrance.
ICSP Neural complements Symantec’s Critical System Protection solution, which Agarwal has described as “an application whitelisting agent that has been remastered from the ground up to provide fixed-function devices cybersecurity without an internet connection.”
Symantec told SecurityWeek that pricing for ICSP Neural starts at $25,000. The product can be ordered now and is expected to ship in early 2019.
“USB devices are given away at events, shared between co-workers, and reused again and again for business and personal use, introducing the risk of accidental or malicious infection. The impact of connecting an infected device to a critical system can be devastating,” said Patrick Gardner, senior VP of advanced threat protection and email security at Symantec. “Behind the scenes, ICSP Neural retrofits existing infrastructure with a central nervous system utilizing artificial intelligence to protect critical infrastructure. On the front end, a rugged aluminum design embodies a simple, intuitive user experience that clearly highlights potential threats.”
Related: Symantec Launches Email Threat Isolation Solution
Related: Symantec Acquires Appthority, Javelin Networks
Related: Symantec Completes Internal Accounting Investigation














