Symantec recently published a blog post detailing two new methods being deployed to avoid malware detection and analytics. According to research, criminals are taking a low-cost / low-tech approach and using sleep loops along with basic monitoring to avoid getting caught.
In their latest Internet Security Threat Report, Symantec noted that some 400 million malware variants were created in 2011. This equates to an average of 33 million a month, which means it is impossible to manually detect and defend against them. To level the field some, security researchers and vendors have developed a wide range of tools in order to automate the process.
Automated detection, often in a Virtual Machine (VM) or with a process and behavior check, has been around for years. Criminals know they are being watched, so they develop malware to avoid these checks. Some of the widely known circumvention techniques used by the criminals include checking for registry entries, video drivers, assembler code of a certain type, process names, and more.
However, Symantec has seen two additional methods being deployed by malware authors that seem to be working to a degree. The first is a subroutine in the malware’s code that monitors mouse communication.
“As a person usually uses a mouse when using Windows, the _main_routine subroutine works fine. But as an automated threat analysis system doesn’t use a mouse, the code remains dormant so an automated threat analysis system may not detect it as malware,” Symantec explains.
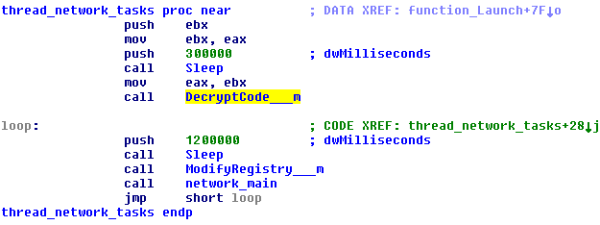
The second method is one of wait and see. The malware runs in parts, executing the first command after waiting for five minutes, then an additional 20 minutes to execute the second command, and finally, 20 minutes more before the final command is run. This enables the malware to avoid detection by applications and systems that only check for a short amount of time.
While somewhat effective, these new tactics aren’t super advanced, and not reserved for elite malware developers.
“In the past, malware authors used very difficult techniques to detect virtual environments. As such, they may have needed specialized skills, such as assembler code writing skills, knowledge of virtual machines, and knowledge of CPUs and memory management,” Symantec explaind. “However, the techniques described in this blog are not technical and hence malware authors these days do not need technical skills to hide their creations from automated threat analysis systems. Furthermore, they are always researching and testing new ideas in order to fool automated threat analysis systems.”

