Israeli startup Sweet Security has emerged from stealth, launched a Cloud Runtime Security Suite, and announced a $12 million seed funding round led by Glilot Capital Partners with angel investors including Gerhard Eschenbach, and Travis McPeak also participating.
The firm, headquartered in Tel Aviv, Israel, was founded in 2022 by Dror Kashti, CEO (former CISO of the Israel Defense Forces – IDF) and Eyal Fisher, CPO (former head of the cyber department at the IDF’s Unit 8200). They were joined by Orel Ben-Ishay, former Head of the Cybersecurity R&D center at Unit 81.
The foundational principle underlying the Sweet Suite (we’ll just call it Sweet) is that while it is important to shift security left in securing development lifecycles, this must not be to the detriment of looking right toward runtime. “Attacks only occur in runtime,” says Sweet, “and companies require technological ‘boots on the ground’ to detect them.” Existing detection tools, it adds, either offer a limited analysis of cloud attacks or aren’t optimized for the cloud. Most were developed to detect on-prem attacks and are simply re-purposed to work on cloud attacks – but cloud attacks differ in pace, volume, and operation.
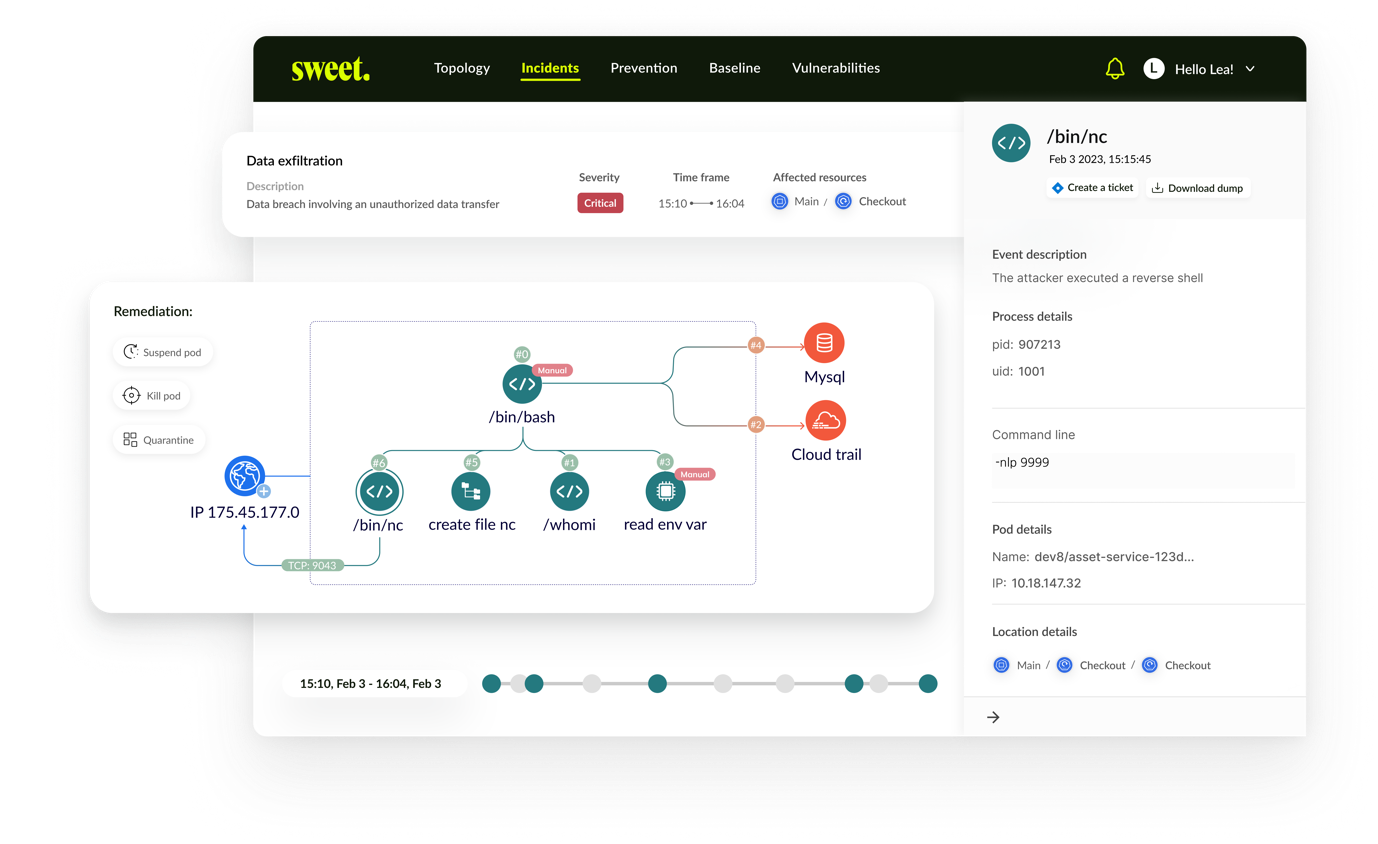
The biggest problem is that many existing detection tools provide too many ‘alerts’ with insufficient context. Alert fatigue is a genuine problem that can lead to missed detections and response opportunities. Kashti cites his inspiration for Sweet coming from frustration in his IDF CISO role: “I was looking for a tool that would help me to detect and respond to cloud attacks – and honestly, I couldn’t find a good solution.”
The Sweet solution is claimed to be new on two primary counts. According to VP of marketing, Noa Glumcher, firstly, it is claimed to be the first solution that combines cloud runtime detection, prevention, and response into a single solution suite. “Secondly,” she adds, “we have a very unique, somewhat innovative framework for detection.” This is a runtime sensor, described as ‘patent pending automatic learning’ rather than machine learning in the now traditional sense. “We start from a behavioral analysis baseline that includes the business logic, the cloud context, and everything specific to the customer’s environment. And we also learn the anomalies.”
This starting point allows three things. “The first,” she continued, “is to showcase everything within your cloud workloads, all the assets, how they’re connected, all their map metadata and all those connections. Another thing is to provide different levels of response automation depending on the customer’s requirements. The third is prioritization. Even before any attack, because we have runtime visibility, we can locate, prioritize, and reduce CVEs by up to 94%.”
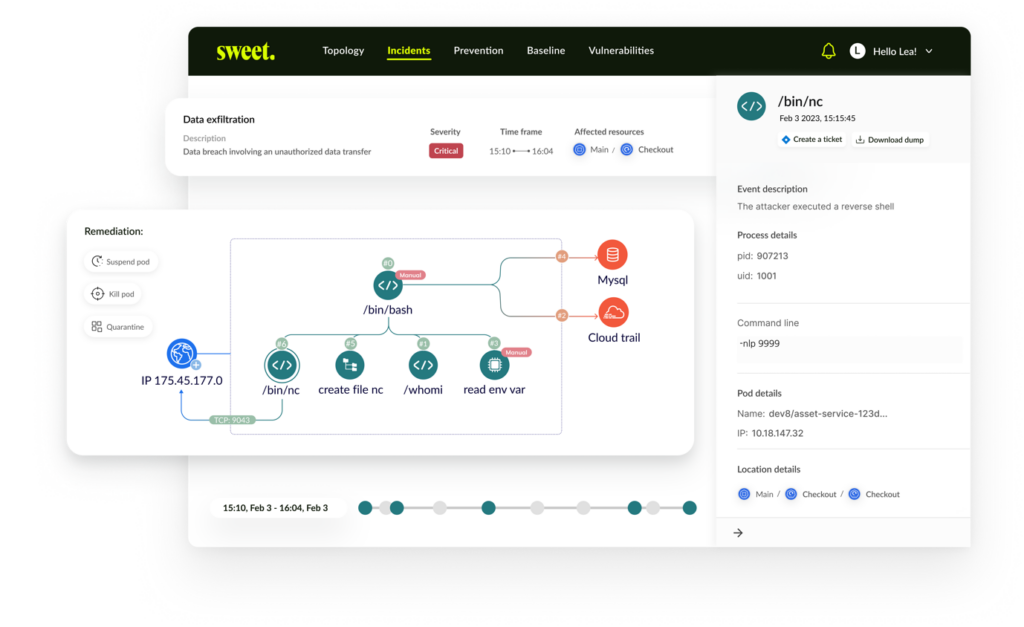
The plan is to build on the possibilities provided by the sensor and its detection capabilities (in part using the new funding). While the sensor already provides contextualized visibility into the system, Glumcher added, “We will provide a forensic analysis for the incident response team so they can immediately see what has happened – with an impact prediction and hardening recommendations for the developers.” The effect is visibility into potential compromise with remediation suggestions, visibility into an actual compromise, and visibility into the potential effect of a compromise.
“‘Cybersecurity’ and ‘delightful’ are not words that normally go hand in hand, but we want our customers to use them in the same sentence when talking about our solution,” said Kashti “We feel our timing is right to make that happen. If SOC and IR teams don’t have to constantly tune their security products or sift through mountains of alerts, they’ll execute at a higher level, and they’ll be happier. Cloud detection and response may be complex, but it doesn’t have to be painful.”
The seed funding will be used to expand the development team, further the company’s R&D efforts, open a US office, and expand its global presence.
Related: Dasera Scores $12M Funding for Cloud Data Security
Related: Entitle Nabs $15M Seed Funding for Cloud Permissions Management Tech
Related: Cisco to Acquire Cloud Security Firm Lightspin for Reported $200 Million
Related: Cisco to Acquire Valtix for Cloud Network Security Tech