PRAGUE – Virus Bulletin 2015 – An analysis of the vulnerabilities discovered in the systems of organizations in various industries provides some insight on the most common types of flaws and the time it takes to address them.
Clint Gibler, a software security engineer at NCC Group’s Domain Services division and the author of the study, detailed the findings on Wednesday at the Virus Bulletin conference in Prague.
Running a commercial scanner on the systems of 100 organizations across ten industry verticals between February 2014 and May 2015 revealed a total of 908,000 security issues. The sectors analyzed by the researcher include charity, energy and utilities, financial services, health, IT, leisure and media, public sector (education and local), retail, and transport.
It’s worth noting that the number of scans, the tools used and the mode in which they were run are different between industries and between companies, which increases the difficulty of making overall statements or generalizations. However, Gibler told SecurityWeek in an interview that the data can be useful for helping organizations determine where they stand compared to others in the same industry.
As part of this research, the systems of the targeted charity organizations underwent roughly 30 scans which led to an average of more than 4,200 findings, just over half of which were classified as true positives after they were manually vetted by a technical account manager. A much larger number of vulnerabilities have been identified in other sectors, but the percentage of false positives was significantly higher in some cases.
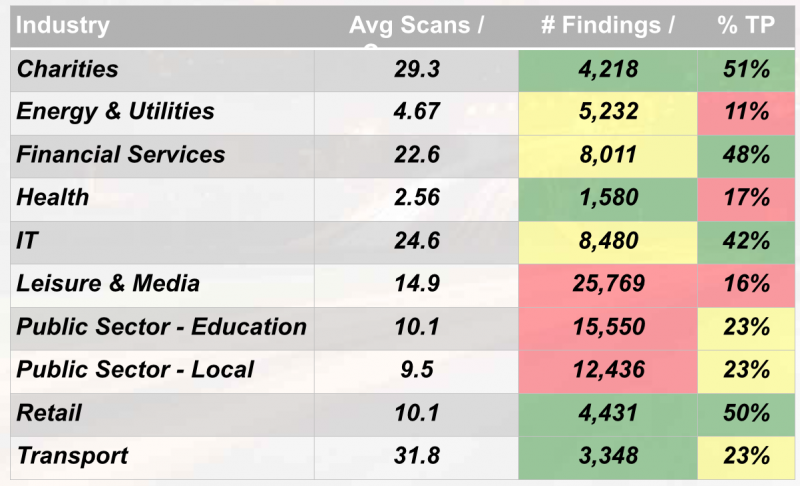
The 49-89 percent false positive rates show that using a managed service that vets scanner reports and removes false positives can be highly valuable for companies as it saves them the time and resources needed to extract useful information from all the noise, Gibler said.
The study found that across all companies, the most prevalent types of issues were related to web application security, particularly flaws affecting the web server or language in which the web application was written. The scans also revealed numerous network issues, mainly related to crypto (SSH, SSL, PKI), and failure to meet web application best practices.
One interesting vertical is the transport industry, where a large majority of the security issues uncovered by the scanners were vulnerabilities impacting the web server or language in which the web app was written.
Once affected companies were notified about the existence of the flaws, the vulnerable Linux packages were all updated within a 20 week timeframe. On the other hand, only 75 percent of Microsoft patches were applied in a similar timeframe, with 10 percent of the Microsoft product issues being left unresolved even after a year.
The researcher discovered that security bugs requiring more environment-specific solutions take longer to fix, and there is a higher chance that they will remain unresolved. These types of issues can include disabling a vulnerable service, reconfiguring default accounts, removing files, and updating configurations.
Overall, issues related to cryptography, such as updating OpenSSL and reconfiguring SSL, have a patching rate of roughly 60 percent within a 30 week timeframe. However, the report points out that such weaknesses are less likely to be resolved compared to other types of issues. As for web applications, over half of the identified vulnerabilities were fixed by affected organizations within ten weeks after learning of their existence.
Overall, the report shows that more than half of the vulnerabilities are generally patched within 10-20 weeks, while the rest are addressed more slowly.
“We feel this intuitively makes sense, as an organization will likely make an initial large push towards addressing the security issues they are informed about. However, the issues that are not resolved in the initial push are addressed slowly, when time permits, over the subsequent months,” Gibler explained.
The study shows a large disparity between industries in the time to fix and the overall percentage of fixed issues. When it comes to host-based vulnerabilities — those related to an operating system, a database, or out-of-date software — the transport industry addressed most of the identified flaws within a ten week period. On the other hand, it took companies in the IT industry 35 weeks to resolve just half of the vulnerabilities.
The transport industry has also been efficient in patching network-related security bugs. However, the report notes that no industry resolved more than 90 percent of network-related issues, and half of the targeted sectors resolved roughly 60 percent of the flaws.
Companies in the transport and health sectors managed to address 90 percent of the web application findings in under ten weeks. At the other end of the chart we find charities, IT firms, public sector organizations, and retailers, which needed 30-50 weeks to address 60-70 percent of the web application vulnerabilities.
“Of all three groups, host-based findings are resolved at the highest rate across industries, followed by web application and lastly network-related findings. As one might expect, the financial services industry resolved one of the highest percentages of findings in each of the categories, though not necessarily the most quickly,” Gibler said.
Each of the identified vulnerabilities was classified based on its CVSS score. However, the report shows that the severity of the uncovered issues does not have a direct impact on the time to fix.
“CVSS score does not appear to have a direct impact on the speed with which a finding is resolved, as in the first 10 weeks, findings with a score of between 3 and 6 are more likely to be resolved than those in the range of 7–10,” the researcher noted. “One potential explanation for this behaviour is that findings with a lower CVSS score are easier to address and are thus resolved quickly, while more serious findings require more effort and are thus addressed more gradually.”
The complete report will become available in the coming days.














