A survey conducted by the Ponemon Institute on behalf of security solutions provider TUV Rheinland OpenSky analyzes the security, safety and privacy challenges and concerns related to the convergence between information technology (IT), operational technology (OT), and industrial internet of things (IIoT).
Industrial systems are increasingly sophisticated and automation plays a critical role in ensuring efficiency, which has led to IT, OT and IIoT systems becoming increasingly integrated. However, there are several challenges and concerns that need to be addressed to achieve convergence.
The study conducted by TUV and Ponemon is based on responses from over 650 individuals from organizations of all sizes, representing sectors such as automotive, oil and gas, energy, healthcare, industrial manufacturing, logistics and transportation, consumer goods and retail, and telecommunications. A vast majority of the companies (99%) have employees in the United States, but many also have employees in Canada (67%), Europe (69%), the APAC region (58%), Latin America (54%), and the Middle East and Africa (35%).
Roughly two-thirds of respondents said they believe IT and OT convergence is a good thing and that it’s being driven by digitalization. Over 60% of respondents believe convergence is important for achieving a more mature security posture, and nearly half believe it’s an important factor for improving the trust and confidence of supply chain partners.
However, according to the study, many believe convergence cannot be achieved without support from the company’s chief information officer (CIO) and other C-level executives. At least half of respondents also said convergence is not possible without strict safeguards for critical operations data, and it’s not possible if the organization has a long history of silos and turf issues.
“Conflicts created by turf and silo issues are a significant organizational barrier to successful convergence. The creation of a cross-functional team to manage cyber risk across IT and OT systems will help eliminate this problem,” the report says.
At least half of respondents claimed their organization is highly effective in achieving various tasks that are crucial for convergence, including safety program management, cybersecurity planning, leadership and governance, security program management, awareness and training, incident preparedness, testing and assessment, and threat and risk analysis. Fewer companies claim to be good in areas such as third-party risk management, compliance with regulations and standards, and privacy program management.
Respondents said they believe resilience, agility, a strong security posture, and expert staff are the most critical factors for ensuring a successful convergence process.
This process is in many cases managed through a combination of in-house and outsourced expertise (46%), followed by only in-house teams (34%), and only external service providers (20%).
When it comes to budgets allocated for convergence, 45% of respondents said they have a budget, but 50% said they do not have a budget for it.
The inability to overcome turf and silo issues has been cited by more than half of respondents as a barrier to the successful convergence of cybersecurity, functional safety and data privacy. Other barriers cited by a significant number of respondents include the inability to control security, safety and privacy initiatives, the inability to secure assets and infrastructure, the inability to ensure the free flow of information, and the lack of in-house expertise.
The lack of skilled employees is considered the most common problem for a strong convergence process, along with insufficient risk assessment.
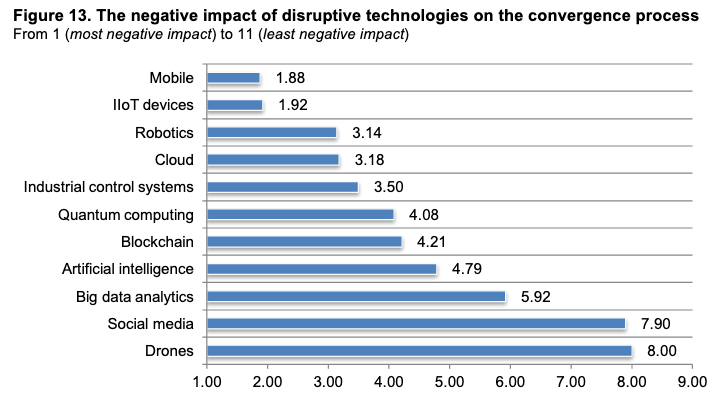
Many organizations believe that mobile and IIoT devices have the most negative impact on convergence.
The study found that while safety objectives are in many cases at least partially aligned with business objectives, privacy objectives and cybersecurity objectives are less likely to be aligned. On the other hand, over 70% said cybersecurity is the most influential to their company’s business strategy, while privacy is the least influential.
While security is considered important during the convergence process, many organizations don’t appear to be able to maintain a strong cybersecurity posture, but they are more confident in their ability to maintain a strong safety posture.
The complete report, “Safety, Security & Privacy in the Interconnected World of IT,OT& IIoT,” is available for download in PDF format.













