Russia’s national vulnerability database is slow, incomplete and it focuses on security flaws that could pose a threat to the country’s IT systems, according to an analysis conducted by threat intelligence firm Recorded Future.
After analyzing the national vulnerability databases of the United States and China, Recorded Future has decided to take a look at Russia’s database, known as the BDU. The BDU is maintained by the Federal Service for Technical and Export Control of Russia (FSTEC), an agency whose role is to protect state secrets and provide support for counterespionage and counterintelligence missions.
Researchers discovered significant differences both in the number of vulnerabilities and the time it takes to add them to the database, compared to the databases run by China and the United States. For instance, while the US’s NVD stored information on nearly 108,000 security holes, the BDU only documented just over 11,000 flaws in March, when Recorded Future conducted its analysis.
As for the time it takes for a vulnerability to be included in the BDU, the average is 95 days, much more than in the United States (45 days) and China (11 days).
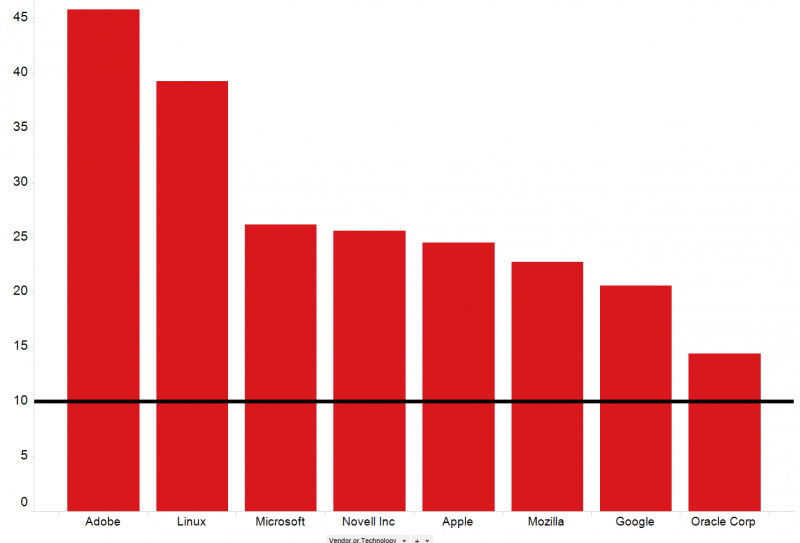
While Russia’s database only covers roughly 10 percent of known vulnerabilities, there are certain pieces of software and certain types of bugs that seem more important to the maintainers of the database.
Researchers noticed that the BDU stores information on 61 percent of the vulnerabilities known to have been exploited by Russia-linked advanced persistent threat (APT) groups in their campaigns. This is in contrast to China, whose CNNVD database hides or delays flaws exploited by the country’s intelligence services.
While the vulnerabilities exploited by Russia-linked APTs affect some of the world’s most widely used software, their presence in the vulnerability database suggests that the systems of the Russian government also run these programs, especially since FSTEC’s mission is to protect government systems. This also provides insight into the applications used by the Russian government.
Moreover, Recorded Future points out it’s also possible that hackers sponsored by the Russian military leverage vulnerabilities in the BDU in their operations, or that the military may be obligated to protect the state’s IT systems by providing information on these flaws.
“The public record and available data is not yet sufficient to determine the relationship between FSTEC and Russian state-sponsored cyber operations,” Recorded Future said in its report.
On the other hand, while the BDU covers many vulnerabilities affecting Adobe products, even in this category the database is incomplete. According to researchers, there are over 1,200 Adobe bugs with a CVSS score higher than 8 that are not present in Russia’s database.
So why waste resources on an incomplete and very slow vulnerability database?
A lack of resources could be an explanation, but analysts note that FSTEC has over 1,100 employees, nearly triple compared to the US’s NIST Information Technology Laboratory (ITL), which maintains the country’s NVD.
Another possible scenario is that FSTEC has both an offensive and defensive mission and its database covers vulnerabilities based on competing needs. However, experts believe this theory is not accurate either considering that the agency is not a public service organization, as its main mission is to protect state and critical infrastructure systems and support counter intelligence initiatives.
The most likely scenario, Recorded Future believes, is that the DBU is “simply a baseline for government information systems security and software inspections.”
One of the roles of FSTEC is to review the software of foreign companies that want to sell their products in Russia. This includes firewalls, antiviruses and applications that use encryption.
“FSTEC is a military organization and is publishing ‘just enough’ content to be credible as a national vulnerability database. The Russian government needs vulnerability research as a baseline for FSTEC’s other technical control responsibilities, such as requiring reviews of foreign software,” the threat intelligence firm said.
Related: Cyber War and the Compromise of Reliable Full Disclosure
Related: The Top Vulnerabilities Exploited by Cybercriminals

