Researchers Discover Vulnerability in Canon’s Original Data Security Kit, Allowing Manipulated Images to Pass as Authentic
Researchers from ElcomSoft Co. Ltd (yes, the makers of popular password cracking and wifi cracking tools) say they have discovered a vulnerability in the way Canon digital cameras validate and authenticate image data to prove image originality, ensuring that images and their meta-data such as geo-location information are unaltered in any way.
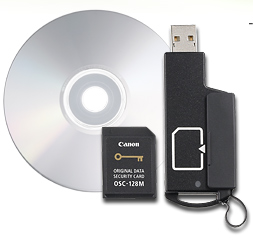
The researchers were able to extract secret keys from the Canon hardware used to calculate authentication data from Canon EOS digital cameras, and use the keys for adding authenticity signatures to a set of manipulated digital images. The images signed with an extracted key come validated as being original and authentic by Canon’s Original Data Security Kit (OSK-E3). The vulnerability opens the possibility to produce images that will be positively validated by Canon’s own Original Data Security Kit (OSK-E3) regardless of whether or not the images are genuine.
Credibility of photographic evidence can be critical in many cases for insurance companies and courts, as they may accept digital image as indisputable evidence if it can be proven genuine, the company says. Additionally, leading news agencies, including the Associated Press, use Canon Original Data Security system as means to ensure image originality and authenticity.
The vulnerability exists in all Canon cameras manufactured to date and having the security feature. According to Elcomsoft, all current cameras are susceptible, including the entire range of consumer cameras (e.g. Digital Rebel XS, also known as EOS 1000D in Europe and Kiss F in Japan), semi-pro and professional series, including the latest EOS-1D Mark IV.
ElcomSoft is not releasing any technical details but has demonstrated the vulnerability with a set of manipulated images successfully passing validation with Canon Original Data Security Kit OSK-E3 at http://canon.elcomsoft.com/ – the company says it has notified Canon and CERT about the vulnerability.














