CrackQ Password Cracking Manager is an Interface for Hashcat Served by a REST API and a JavaScript Web App
Hashcat is billed as the world’s fastest password cracker. It uses the power of graphical processing units (GPUs) to compare guessed plaintext passwords with known password hashes at high speed — often at hundreds of billions of guesses per second — until a match is found. It has become an important tool for red teamers and pentesters analyzing the strength of customers’ passwords.
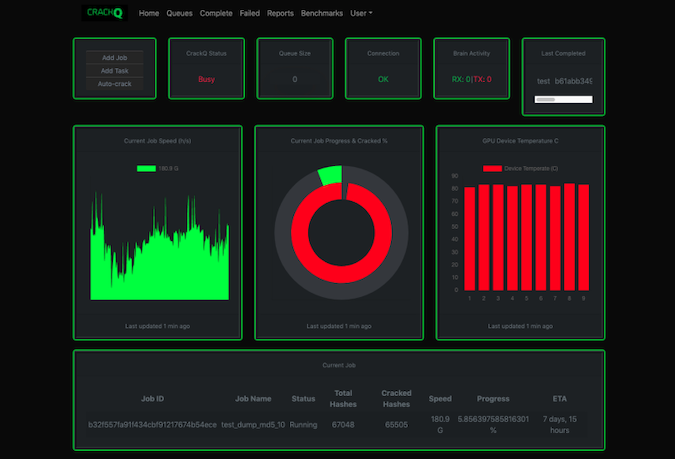
But like all such raw tools, users can benefit from additional features and improved operational management. At Black Hat Europe in London, UK, cybersecurity and managed security services provider Trustwave has announced the release of CrackQ (alpha version), available from GitHub. Developed over the last year by Trustwave principal security consultant Dan Turner, CrackQ, he says, is “an intuitive interface for Hashcat served by a REST API and a JavaScript front-end web application for ease of use.”
Never quite content with the cracking rigs he has used, Turner started to develop his own — initially just wanting something written in Python so that he could add additional features as required. But the project grew into CrackQ, a Hashcat password cracking manager. The ability to add additional features remains. Turner has “a multitude of useful features planned for future releases”, and also hopes the GitHub community will assist with future development.
It doesn’t use shell commands to interface with Hashcat but does so directly through the libhashcat library using PyHashcat C bindings. It uses SAML2 authentication allowing the use of MFA, and can alternatively use LDAP. But while the current version includes features not found elsewhere, other systems have options not yet available in CrackQ.
“For example,” says Turner, “it currently is not able to work as a distributed system, rather it’s a client-server setup. This is mainly because distributed cracking is not what we needed at this time, but it’s an API so this could be added quite easily in the future if I decide to go down that road.”
Turner has also created a password analysis library, called Pypal — so named as a hat-tip to the command line analysis tool Pipal developed by independent security consultant and researcher Robin Wood. It provides largely similar analyses but delivers graphical results, and will on demand generate a report from the results of a cracking job. The report will highlight insecure password choices, allowing security teams to eradicate weak passwords from among company staff.
Another useful feature is integration with Hashcat Brain which is automatically engaged when it is efficient to do so. Brain checks to see if a given password has already been checked, preventing repeated retries during different cracking runs, and improving efficiency for slower algorithms. “However,” explains Turner, “the brain becomes the bottleneck when cracking at higher speeds. It has a bottleneck of around 500kH/s so CrackQ will check the speed for the selected algorithm and engage the brain when it’s effective to do so.”
CrackQ can be considered a work in progress that is already usable. “For us,” says Turner, “every penetration test with a significant password store compromise will include a detailed report analyzing weak areas in a password policy. CrackQ will help to visualize that and perhaps help drive home the message about poor password choices.”
Related: Password Cracking Tool Hashcat Goes Open Source
Related: New Method Discovered for Cracking WPA2 Wi-Fi Passwords
Related: The Enduring Password Conundrum
Related: UK’s NCSC Suggests Automatic Blocking of Common Passwords












