Cybersecurity vendor Palo Alto Networks is calling urgent attention to a remote code execution vulnerability in its GlobalProtect portal and gateway interfaces, warning that it’s easy to launch network-based exploits with root privileges.
The Santa Clara, Calif.-based Palo Alto Networks said the security defect can be exploited to allow an unauthenticated network-based attacker to disrupt system processes and potentially execute arbitrary code with root privileges.
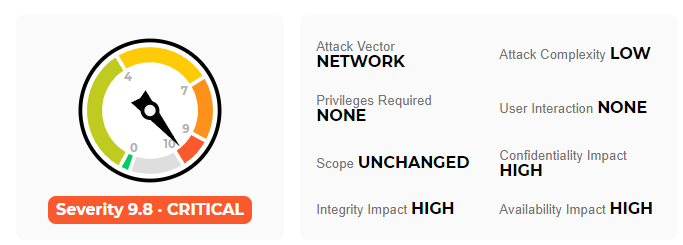
The company slapped a critical-severity rating on the CVE-2021-3064 vulnerability and noted that an attacker must have network access to the GlobalProtect interface to exploit this issue.
Palo Alto said the issue impacts PAN-OS 8.1 versions earlier than PAN-OS 8.1.17. High-priority patches have been issued for enterprise customers running PAN-OS 8.1.17 and all later PAN-OS versions.
The company said it was not aware of any malicious exploitation of this issue but confirmed that attack surface management firm Randori had fitted successful exploits into its red-teaming software product.
[ READ: Zero-Days Under Attack: Microsoft Plugs Exchange Server, Excel Holes ]
According to a vulnerability report from the Randori Attack Team, the vulnerability affects PAN firewalls using the GlobalProtect Portal VPN and allows for unauthenticated remote code execution on vulnerable installations of the product.
“Our team was able to gain a shell on the affected target, access sensitive configuration data, extract credentials, and more. Once an attacker has control over the firewall, they will have visibility into the internal network and can proceed to move laterally,” Randori said.
The company is withholding technical details on the vulnerability for 30 days to allow Palo Alto Networks customers to apply available fixes.
Related: VMware Calls Attention to High-Severity vCenter Server Flaw
Related: US Cyber Command: Foreign APTs Will Exploit Palo Alto Bug
Related: Google Triples Bounty for Linux Kernel Exploitation















