Trend Micro on Wednesday released a new report describing the threats affecting industrial control system (ICS) endpoints in 2020.
According to the report, ransomware infections saw a significant increase last year, mainly due to a rise in Sodinokibi (REvil), Ryuk, Nefilim and LockBit attacks launched between September and December.
The highest number of organizations that had their industrial systems hit by ransomware was seen by the cybersecurity firm in the United States, far more than in any other country. However, in terms of the percentage of organizations affected compared to the total number of organizations in the country, the U.S. was at an average level — the most impacted appear to be Vietnam, Spain and Mexico.
The report is based on data collected from ICS endpoints used to design, monitor and control industrial processes. These systems run industrial automation suites or serve as engineering workstations (EWS).
“Ransomware in ICSs can cause the loss of view or control of physical processes,” Trend Micro explained in its report. “Monitoring and control interfaces such as HMIs and EWS are reliant on image files (.jpg, .bmp, .png) and configuration files to render the interface; However, in ransomware attacks, data including configuration files and images end up encrypted, and therefore, unusable by the ICS software. Therefore, ransomware effectively cripples the HMI and EWS. This in turn leads to productivity and revenue losses for the facility.”
Learn more about vulnerabilities in industrial systems at SecurityWeek’s 2020 ICS Cyber Security Conference and SecurityWeek’s Security Summits virtual event series
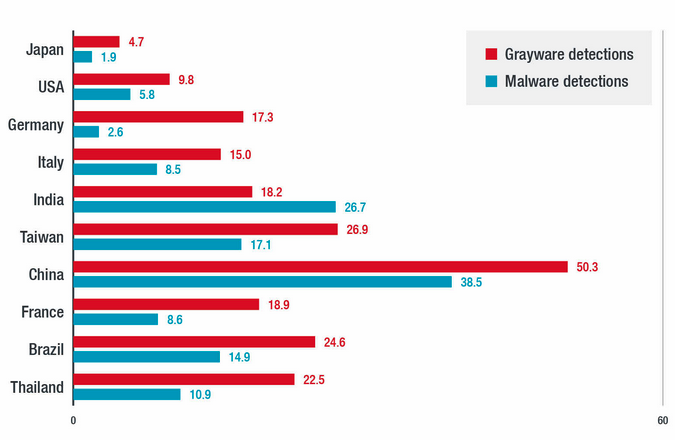
When it comes to malware in general, the highest percentage of malware and grayware detections were observed in China, India, Taiwan, Brazil, Thailand, Italy, France, the U.S., Germany and Japan.
The report also dives into cryptocurrency miner infections detected on ICS. The malware named MALXMR was the most widespread, and the highest percentage of detections was in India, which also topped the chart for WannaCry infections.
Trend Micro also reported finding legacy malware in a small percentage of organizations, including Sality, Ramnit, Autorun, Gamarue, Virux, and others.
Conficker (Downad), a worm that has been around since 2008, was also still detected on hundreds of ICS endpoints.
Related: Pandemic Leads to Rise in Industrial Systems Targeted Via RDP
Related: Over 12% of ICS Security Incidents Attributed to Nation-State Hackers
Related: Number of ICS Vulnerabilities Continued to Increase in 2020
















