A known ransomware group has taken credit for the recent cyberattack targeting Nissan and claims to have stolen 100 Gb of information from the Japanese car manufacturer.
The carmaker revealed in early December that internal systems belonging to Nissan Motor Corporation and Nissan Financial Services in Australia and New Zealand had been targeted by hackers.
It confirmed on December 22 that an “unauthorized third party illegally accessed some of the company’s network systems in Australia and New Zealand” and said it has been working on determining what information is impacted.
Cybersecurity agencies in Australia and New Zealand, as well as privacy regulators and law enforcement, have been notified.
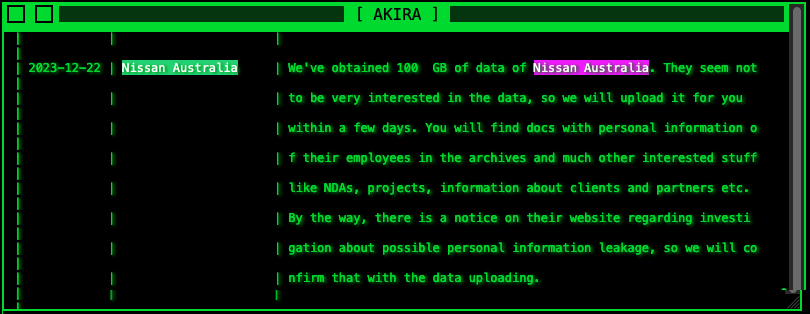
A ransomware group named Akira has taken credit for the attack on Nissan, claiming to have stolen 100 Gb of data, including corporate files and personal information belonging to employees.
The cybercriminals are threatening to leak the data in the coming days, suggesting that Nissan is not willing to pay the ransom they have demanded.
The Akira ransomware operation emerged in March and is believed to have some links to the notorious Conti group. Akira has targeted roughly 180 organizations to date, mostly in the United States.
Nissan is not the only car manufacturer targeted by cybercriminals in recent months. Toyota Germany has also notified customers of a data breach involving their personal information following a ransomware attack.
Related: 25k Nissan Customers Affected by Data Breach at Third-Party Software Developer
Related: Yamaha Motor Confirms Data Breach Following Ransomware Attack
Related: Toyota Discloses New Data Breach Involving Vehicle, Customer Information


